In 2021, the number of companies affected by ransomware skyrocketed. In 2022 it will be worse: here are the latest statistics on computer attacks.

Fast & Guaranteed Recovery
HelpRansomware provides a 100% guaranteed ransomware removal and data recovery service, with 24/7 worldwide assistance.
What are computer attacks?
A computer attack or cyberattack is a malicious action by third parties whose objective is to access a system to steal private informations.
There is a wide typology of computer attacks hijacking data, such as Trojans, doxing, or ransomware attacks.
The National Institute of Standards and Technology (NIST) of the United States Government defines computer attacks as follows:
“An attack, via cyberspace, targeting an enterprise’s use of cyberspace for the purpose of disrupting, disabling, destroying, or maliciously controlling a computing environment/infrastructure; or destroying the integrity of the data or stealing controlled information.”
How does a computer attack happen?
The Spanish National Institute of Cybersecurity (INCIBE) explains in seven phases how a computer attack occurs:
- Reconnaissance: The cybercriminal collects information about their target.
Look at the organization’s details in the open and look for information about the technology it uses.
The attacker assesses which attack methods might work;
- Target-specific preparation: For example, an attacker could create a PDF and include it in an email that impersonates a legitimate person with whom the company interacts typically;
- Distribution: transmission of the attack, for example, by opening an infected document sent by email;
- Exploitation: it is understood as the detonation of the attack, compromising the computer and its network.
It is usually produced by exploiting a known vulnerability for which there is already a security patch, which, if not patched, would allow computers to be entered from the outside;
- Installation: The attacker installs the malware on the victim or steals the credentials;
- Command and control: the cybercriminal manages the victim’s system and starts to perform malicious actions such as stealing confidential documents or installing other programs;
- Actions on targets: expand the malicious activity to more targets.
In the case of ransomware, it includes information encryption and the demand for an economic ransom from the victim.
The business of ransomware extortion
Before we start with the statistics, it should be clear that ransomware is a business whose primary purpose lies in extortion; as Microsoft explains:
“Ransomware is a type of extortion attack that encrypts files and folders, preventing access to important data. Criminals use ransomware to extort money from victims by demanding money […] in exchange for not releasing sensitive data to the dark web or the public internet.”

In 2021, 59% of attacks used a double extortion strategy, as explained in the X-Force Threat Intelligence Index report by IBM Security.
HelpRansomware always stresses the importance of not paying the ransom cybercriminals demand.
Furthermore, OFAC and FinCEN have illegally declared paying for it:
“Companies that facilitate ransomware payments encourage future ransom demands and may also risk violating OFAC regulations.”
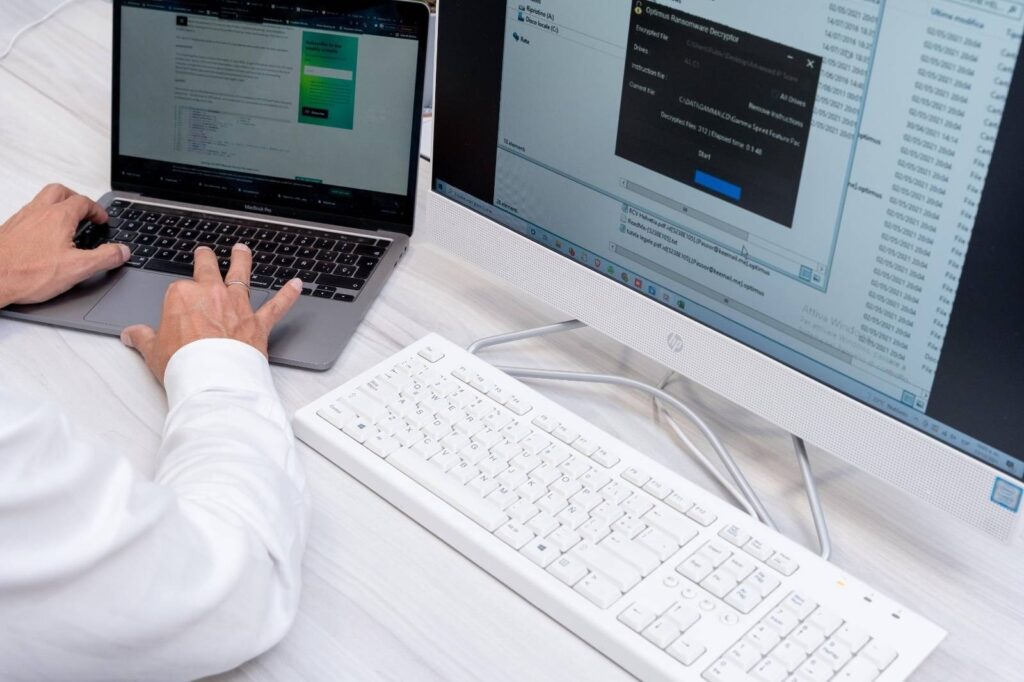
The best option is to contact a company specialized in recovering encrypted files.
HelpRansomware company is an expert in ransomware removal, cybersecurity, and decryption.
100 statistics of computer attacks and ransomware
Below, you will learn the 100 worldwide most influential and recent statistics on computer attacks and ransomware.
39% of organizations were damaged by a cyber incident
The Global Cybersecurity Outlook 2022 report from the World Economic Forum indicates that 39% of organizations have been affected by a third-party cyber incident in the last two years.

55% of SMEs have experienced a cyber attack
In 2020, 55% of small and medium businesses experienced a cyber attack, according to the World Economic Forum.
88% of respondents expressed concern about the resilience of SMEs within their ecosystem.
39% of cyber leaders affected by an incident
Continuing with the previous report, the vulnerability of the business ecosystem is analyzed.
The result shows that 40% of cyber leaders have been affected by an incident caused by a third party within their ecosystem.
The value of the shares falls by -3.50%
Fourteen days after making a cyber breach public, the average share price ‘bottoms out’ and underperforms (-3.50%) the NASDAQ.
After six months, the average share price falls -3% against the performance of the NASDAQ.
The cost for a cyber incident is $3.6 million
Continuing with the statistics on computer attacks, the World Economic Forum report indicates that the cost of breaches for an organization is high.
The value amounts to an average of 3.6 million dollars per cyber incident.

Ransomware attacks grew by 151%
Ransomware attacks saw a significant increase in the first six months of 2021.
The global volume of attacks grew by 151%.
FBI warns of the existence of 100 strains of ransomware
The US Federal Bureau of Investigation (FBI) has warned that there are currently one hundred different strains of ransomware in circulation worldwide.
There were 270 attacks per organization
In 2021, there was an average of 270 attacks per organization.
This data represented an increase of 31% compared to 2020.
The ACSC responded to 2,266 cybersecurity incidents
The Australian Cyber Security Centre (ACSC) report summarizes the top cyber threats and statistics between July 1, 2019, and June 30, 2020.
Throughout this analysis, the ACSC responded to 2,266 cybersecurity incidents.
A cybercrime report every 10 minutes
Continuing with the previous statistics on computer attack reports, in 2020, the ACSC generated 59,806 cybercrime complaints.
An average of 164 reports per day, or one every 10 minutes.

This is a decrease compared to the previous year, in which 64,567 complaints were registered between July 1, 2018, and June 30, 2019.
4,500 malicious emails per day
At its peak, the ACSC detected more than 4,500 malicious emails per day, including nearly 50 variations, used to infect systems.
The most used cybercrime is fraud
The previous attacks, registered by the ACSC, are distributed in the following categories:
- Image abuse online: 3.52%;
- Devices: 2.25%;
- Fraud: 39.68%;
- Cyber abuse: 22.15%;
- Identity crime: 32.40%.
Out of all the cybercrimes, it is extracted that cyber abuse is the most used by hackers.
37% of organizations, victims of ransomware
Sophos’ 2021 report indicates that 37% of organizations surveyed were victims of a ransomware attack in that same year.
Ransomware encrypted data in 54% of attacks
Continuing Sophos data on cyberattack statistics, 54% of those affected by ransomware in 2021 confessed that cybercriminals managed to encrypt their data.
96% of victims recovered their data
According to the Sophos study, 96% of the victims, whose data was encrypted, recovered their information after the ransomware attack.

Fast & Guaranteed Recovery
HelpRansomware provides a 100% guaranteed ransomware removal and data recovery service, with 24/7 worldwide assistance.
Medium companies pay $170,404 for ransom
According to the Sophos report, the average ransom paid by midsize organizations to open encrypted files was $170,404 in 2021.
65% of data was restored after paying the ransom
The Sophos study indicates that organizations that paid the ransom only recovered 65% of encrypted files, leaving more than a third of their data inaccessible.
29% reported that 50% or less of their files were restored, and only 8% recovered all of their data.
Neutralizing ransomware costs $1.85 million
The average bill to neutralize a ransomware attack, taking into account downtime, people, device and network cost, ransom paid, etc., is $1.85 million.

Extortion attacks have grown by 4%
Ransomware-type attacks, in which data is not encrypted, but a ransom is demanded, have doubled from 2020 to 2021, from 3% to 7%.
The distribution and transport sector is the most resistant
In 2021, the industry best able to prevent attackers from encrypting files was distribution and transportation (48%), followed closely by the media, leisure, and entertainment (47%).
Local government is the most vulnerable sector
Continuing the above statistics on computer attacks, local government is the sector where organizations are most likely to have their data encrypted in a ransomware attack (69%).
Payment in organizations with 100 to 1,000 employees
In 2021, the median ransomware ransom payout for organizations with 100 to 1,000 employees was $107,694.
Payment in organizations with 1,000 to 5,000 employees
Last year, the average ransomware ransom paid by organizations with 1,000 to 5,000 employees was $225,588.
Italy, the country with the highest ransom payments
According to the Sophos report about statistics on computer attacks, the two highest ransom payments were reported by respondents from Italy.
Additionally, the median ransom payment in the US, Canada, UK, Germany, and Australia was $214,096, 26% higher than the global average.
India, the country with lower ransom payments
In 2020, the median ransom payment in India was $76,619, less than half the global figure.
32% of companies paid to recover their data
32% of companies paid the ransom to recover their data from a ransomware attack.
This figure represents an increase of 26% compared to 2020.
NGOs, agencies, and entities, threat targets
The 2021 analysis of the National Cryptologic Center (CCN) of Spain explains that 90% of the targets of threats have been public bodies, NGOs, and social policy entities or international affairs.
Ransomware attacks grew by 435%
The Global Risks of 2022 of the World Economic Forum about statistics on computer attacks explains that the ransomware attack grew by 435% in 2020.
Human errors cause 95% of problems
Continuing with the World Economic Forum data, the organization emphasizes that 95% of cybersecurity problems are the result of human error.
And insider threats (intentional or accidental) account for 43% of all breaches.

Expert Ransomware Removal
Our certified professionals have over 25 years of experience in ransomware removal, data recovery, and computer security.
Malware grew 358% in 2020
The Global Risks report indicates that malware threats grew by 358% in 2020.
100 attempts to perpetrate cybersecurity in one minute
In December 2021, just one week after discovering a security flaw in a widely used software library (Log4j), more than 100 attempts to exploit the vulnerability were detected every minute.
This data illustrates how open source encryption can spread vulnerabilities widely.
85% of experts concerned about ransomware
85% of the World Economic Forum leaders have highlighted that ransomware is becoming a growing threat and a significant concern for public security.
A fraudulent transfer of $35 million
The World Economic Forum report about statistics on computer attacks explains an example of the actions of cybercriminals.
They came to clone the voice of a company director to authorize the transfer of 35 million dollars to fraudulent accounts.
Bank fraud increased by 117% in the UK
In 2021, UK internet banking fraud increased by 117% in volume and 43% in value compared to 2020, as people spent more time shopping online.
Cyber insurance increased by 204% in the US
In the United States, cyber insurance prices increased 96% in the third quarter of 2021, marking the most significant growth since 2015 and a year-over-year increase of 204%.
Credential theft in 85% of violations
KnowBe4‘s report about statistics on computer attacks indicates that cybercriminals stole login credentials in 85% of social engineering-related breaches.
Phishing incidents doubled in a year
Phishing incidents nearly doubled in frequency from 2019 to 2020.
According to the FBI, they went from 114,702 incidents in 2019 to 241,324 incidents in 2020.
Phishing grew by 6,000% as a result of Covid-19
The KnowBe4 report acknowledges a 6,000% increase in phishing attacks related to Covid-19 in March 2020 alone.

83% of companies attacked via phishing
83% of businesses and 79% of charities reported phishing attacks in 2021, according to the UK Government’s Department for Culture, Media and Sport (DCMS).
60% of Group-IB cases associated with ransomware
In 2021, more than 60% of all incidents investigated by Group-IB involved ransomware.
23% of incidents correspond to ransomware
According to the IBM Security report about statistics on computer attacks, ransomware was the most popular attack method in 2020, making up 23% of all incidents.
Sodinokibi made $123 million in profits in 2020
Sodinokibi ransomware actors, also known as REvil, alone made at least $123 million in profits in 2020 and stole around 21.6 terabytes of data.
Scanning and exploitation of vulnerability, first vector
Vulnerability scanning and exploitation jumped to the top of infection vectors in 2020, overtaking phishing, the principal vector in 2019.
100 executives in a phishing campaign
In mid-2020, a global phishing campaign targeted more than 100 senior executives in management and procurement roles related to the coronavirus.
56 new Linux-related malware families
In 2020, 56 new Linux-related malware families were discovered, the highest number ever.
According to the IBM Security report, this figure represented a year-on-year increase of 40% compared to 2019.
Immediate Ransomware Help
Don’t let ransomware hold your business hostage. Our experts are ready to recover your data and secure your systems.
In 2020, 31% of targets went to Europe
Europe was the most attacked continent in 2020, experiencing 31% of attacks, followed by North America (27%) and Asia (25%).
A year earlier, the North American region suffered 44% of the cases.
Organizations in the Middle East and Africa experienced 8% of attacks, up slightly from 7% in 2019.
Attacks on the financial sector, through servers
According to the IBM Security report, in 2020, 28% of attacks on the finance and insurance sector were through access to servers.
10% of attacks on the financial sector are ransomware
In 2020, 10% of attacks on the financial sector came from ransomware.
21% of attacks on the manufacturing industry, ransomware
In 2020, 21% of attacks against the manufacturing industry came from ransomware.
35% of attacks on the energy sector, data leakage
35% of attacks on the energy industry were data theft and leak attempts.
In 2020, this sector was positioned as the third most attacked, compared to ninth place the previous year.
33% of attacks on governments are from ransomware
The IBM Security report indicates that 33% of government attacks were ransomware, the second-highest percentage of all sectors.

Similarly, 25% correspond to attempted theft and data leakage.
90% of DNS thefts target media
90% of malicious DNS thefts (a domain name is deceptively similar to a legitimate web page) target the media.
Double extortion has grown by 935%
The Group-IB report also indicates that double extortion attacks have increased by 935%.
This typology consists of first encrypting the files and then creating a backup copy of the confidential data.
Software bugs grew 21% in 2021
According to HackerOne‘s report about statistics on computer attacks, hackers reported 66,547 software bugs in 2021, 21% more than in 2020.
Without automatic security: $6.71 million cost
The Cost of a Data Breach report from IBM Security differentiates costs between organizations with security automation and those that do not have it.
On the one hand, companies without security automation experienced breach costs of $6.71 million in 2021.
On the other hand, for organizations with security automation, 2.90 million dollars.
$590 million in suspicious activity
FinCEN examined ransomware-related SARs (Suspicious Activity Reports) filed between January 1, 2021, and June 30, 2021, to determine trends.
The dataset illustrated 635 SARs reporting $590 million in suspicious activity related to ransomware.
This figure represented an increase of 42% compared to 416 million dollars for the whole of 2020.
Of the 635 SARs filed during the review period, 458 report actual transactions that occurred during the review period worth $398 million.

Expert Ransomware Removal
Our certified professionals have over 25 years of experience in ransomware removal, data recovery, and computer security.
The financial sector is the most affected by phishing
In the first quarter of 2021, the online industry most affected by phishing attacks was the financial institution (24.9%), followed by the media (23.6%) and webmail (19.6%), according to statistics from Statista.
31% of companies suffer attacks every week
In March 2022, the UK Government reported that almost one in three businesses (31%) and a quarter of charities (26%) are attacked once a week.
The DCMS revealed that the frequency of cyber attacks is increasing.
Nearly a third of charities (30%) and two in five businesses (39%) reported cybersecurity breaches or attacks in the last twelve months.
The National Cyber Security Center (NCSC) is not aware of any current specific threats to UK organizations concerning the events in Ukraine but urges businesses to protect themselves against cyber threats.
16,000 sextortion complaints in half a year
As of July 31, 2021, the FBI IC3 received more than 16,000 sextortion complaints, with losses exceeding $8 million.
One in five companies would pay the ransom
According to Thales‘ 2022 report about statistics on computer attacks, one in five companies have already paid or would be willing to pay a ransom for ransomware attacks.

43% of senior bosses experience increased attacks
43% of senior managers, 46% of mid-level managers, and 45% of freelancers reported an increase in cyber-attacks compared to the previous year.
50% of companies do not have an anti-ransomware plan
50% of companies with revenues over $1 billion do not have a formal anti-ransomware plan.
50,000 cases of cybersquatting
According to the World Intellectual Property Organization (WIPO), in 2020, more than 50,000 cases of cybersquatting (the creation of fake websites) were recorded.
87% of infrastructure sectors, victims of ransomware
The Joint Cybersecurity Advisory document, together with other organizations such as the National Security Agency, indicates that fourteen of the sixteen infrastructure sectors (87.5%) in the United States suffered a ransomware attack in 2021.
600 healthcare organizations affected by ransomware
The American Association of Medical Colleges (AAMC) reports that more than 600 US healthcare organizations and more than 18 million medical records have been affected by ransomware.
A Sodinokibi attack affects 1,000 companies
In late 2021, an INTERPOL-coordinated investigation triggered the arrest of many hackers responsible for the Sodinokibi ransomware attacks.
The main problem with this typology is that it uses Raas technology.
This means that it continuously develops new versions and configurations.
In July of last year, an attack involving more than 1,500 affiliates was launched, affecting 1,000 companies simultaneously.
Avaddon, the most damaging ransomware
The program of the United States Department of Health and Human Services (HHS) highlighted that the Avaddon ransomware was the one that had the most impact at the beginning of 2021 worldwide. Conti and REvil followed.
Fast & Guaranteed Recovery
HelpRansomware provides a 100% guaranteed ransomware removal and data recovery service, with 24/7 worldwide assistance.
Conti, the most prevalent ransomware in the United States
Continuing with the previous data and only in the country of the United States, Conti was the ransomware that produced the most incidents in early 2021.
Next, Avaddon Ransomware and Mespinoza/Pysa Raas Operator.
California medical industry most targeted by ransomware
Continuing with the statistics on computer attacks, the medical sector of California, Texas, Georgia, Illinois, and Louisiana is the most affected by ransomware, according to the HHS program.
Eight URLs and 5 weekly fraudulent IPs
The Computer Security Incident Response Team (CSIRT) of the Ministry of the Interior and Public Security of Chile located weekly eight fraudulent URLs, 249 patches for vulnerabilities, and 5 IPs warned in phishing and malware campaigns.
808 million Verifications.io data breach
The European Union Agency for Cybersecurity (ENISA) report ranked the prior data leak incidents in fifteen months.
In the first place, 808 million data breach records on Verifications.io.
Subsequently, the MEGA cloud service with 770 records.
67% of malware was delivered over encrypted HTTPS
Another data that stands out in the ENISA report is that 67% of the malware was delivered through encrypted HTTPS connections.
Six months to detect a data breach
ENISA indicates that six months is the average needed to detect a data breach.
71% of malware spreads between employees
71% of organizations that have suffered a malware attack have witnessed the activity spread from one employee to another.

NCSC handled 777 incidents in 2021
The NCSC Annual review 2021 indicates that the organization expanded its online defense in the UK by managing 777 incidents in 2021 compared to 723 the previous year, with around 20% of organizations linked to the health sector.
Since 2016, the organization has coordinated the UK response to 3,305 incidents (annual totals of 590, 557, 658, 723, and 777).
The NCSC received 5.4 million malicious tips
The NCSC Suspicious Email Reporting Service received 5.4 million reports of potentially malicious material.
This resulted in the removal of over 50,500 scams and over 90,100 malicious URLs.
$70 million lawsuits to recover data
According to the NCSC, the Florida-based company, Kaseya, was attacked by a group of hackers, who seized the data and demanded $70 million in cryptocurrency.
39% of British companies, victims of an attack
39% of UK businesses reported a cyber breach or attack in 2020/2021, compounding a challenging year for many SMEs.
16.4 billion security advice
In 2021, the NCSC provided expert advice to the strategically important space sector (valued at £16.4bn) to ensure that future launch facilities are safe from outside interference.
16% of citizens improved their online security
Continuing with the NCSC report, the data indicates that 16% of British citizens and 8% of micro-enterprises and the self-employed began an activity to improve security in December 2020.
Tunisia, the country most attacked by ransomware
Kaspersky’s real-time ransomware map updates all malicious malware-related activity in the world with the latest data.
Tunisia, Afghanistan, and Serbia are the three countries historically being the most attacked by ransomware.
The cost for ransomware in Canada: $6.35 million
The Canadian Center for Cyber Security reports that in Canada in 2021, the estimated average cost of a data breach, including ransomware, was CAD$6.35 million.
235 annual ransomware incidents in Canada
The Canadian Center for Cyber Security was aware of 235 ransomware incidents against Canadian victims from January 1 to November 16, 2021.
More than half of Canadian victims are from critical infrastructure
More than half of the Canadian victims were critical infrastructure providers, such as energy, health, and manufacturing.

Fast & Guaranteed Recovery
HelpRansomware provides a 100% guaranteed ransomware removal and data recovery service, with 24/7 worldwide assistance.
65% of data breaches target people
The Office of the Australian Information Commissioner (OAIC) report, between January and June 2021, extracts the following data.
65% of data breaches affected 100 groups or less, while 95% targeted individuals.
43% of breaches are due to security incidents
Continuing the data above, the bureau indicates that 43% of all data breaches (192 notifications) were due to cybersecurity incidents.
8% of users fail to use BCC
Human errors have the following causes:
- 40% of personal information is sent by email to the wrong recipient;
- 8% fail to use BCC when sending email;
- 23% carry out an unintentional publication;
- 7% of personal information is sent to the wrong recipient.
This information comes from the OAIC report related to statistics on computer attacks.
289 notifications of malicious or criminal attacks
Malicious or illegal attacks remain the leading source of data breaches, accounting for 289 notifications submitted between January and June 2021 to the OAIC.
10.18% of computers suffered a malware attack
During the year 2020, 10.18% of the computers of Internet users in the world suffered, at least once, a malware-class web attack, according to the Kaspersky security bulletin.
Cryptominers attacked 1,523,148 users
In the period analyzed by Kaspersky, crypto miners attacked 1,523,148 unique users.
Zbot, the financial malware with the most remarkable presence
In 2020, the three financial malware families present in the online environment were Zbot, Emotet and CliptoShuffler.
In 2020, Trojans encrypted 549,301 users
During the period covered by the report, crypto Trojans attacked 549,301 unique users.

Among them, 123,630 corporate users, not counting SMEs, and 15,940 associated with SMEs.
Bangladesh, Mozambique, and Turkmenistan were the countries most affected by this type of malware.
Trojan-Downloader.OSX.Shlayer.a, the biggest threat to macOS
The top three threats to macOS in 2020, were as follows:
- Trojan-Downloader.OSX.Shlayer.a;
- Monitor.OSX.HistGrabber.b;
- AdWare.OSX.Pirrit.j.
Spain, France, and Canada were the three countries with the highest percentage of attacked users.
The malicious URL, the most used program to attack
Continuing with the Kaspersky bulletin, the three most used malicious programs in online attacks are the following:
- Malicious URL;
- Trojan.Script.Generic;
- Trojan.Multi.Preqw.gen.
The malicious URL has a higher percentage than the rest of the programs, reaching 66.07%.
Four out of ten emails about Covid were spam in 2020
Bitdefender‘s 2020 report indicated that that year, four out of ten emails related to the topic of Covid-19 were spam.

450,000 harmful programs daily
The Independent IT-Security Institute (AV-Test) registers more than 450,000 new malicious programs daily.
Every day, the institution updates the data to share the total amount of malware.
1.349 million malware in 2022
Continuing with the AV-Test record, the institution collected 1,349.50 million malware in 2022.
March 2021, the month in which the most malware was registered
Of the last two years, March 2021 is when the newest malware was recorded, with 19.20 million.
2020, the year malware headed for MacOS
2020 was when malware stood out in MacOS (From 58,207 in 2019 to 673,743 registrations).
For its part, in Windows, it happened in 2021, with 116.87 million compared to 90 million in 2020.
HelpRansomware, the world leader in ransomware removal
For over 25 years, HelpRansomware has removed ransomware through its offices in Europe and the Americas.

Immediate Ransomware Help
Don’t let ransomware hold your business hostage. Our experts are ready to recover your data and secure your systems.
In this entire period, more than 75,000 different types of ransomware have been blocked and removed.
The team has analyzed, decrypted, and recovered more than 10 million terabytes of encrypted data.
If you are a victim of ransomware, contact the company, which offers 24/7 global support worldwide.
How to prevent computer attacks?
The Ready site, from the US Department of Homeland Security, has compiled an interesting list on how to prevent computer attacks:
Limit the personal information that is shared online;
- Keep software and operating systems up to date;
- Create strong passwords;
- Do not click on suspicious links;
- Use a secure Internet connection;
- Regularly review account data and credit reports;
- Use antivirus, antimalware, and firewalls to block threats;
- Make a security copy.
In case you have suffered a ransomware attack, quickly contact HelpRansomware.
The company is an expert in ransomware removal, cybersecurity, and decryption.
Their team assists 24/7, guaranteeing ransomware removal and data recovery.
Conclusions
You have discovered the most exciting and impressive statistics on computer attacks through this guide.
The article concludes with some of the most important:
- 55% of SMEs have experienced a cyber-attack;
- The cost for a cyber incident is $3.6 million;
- Ransomware attacks grew by 151%;
- There is a cybercrime report every ten minutes;
- 4,500 malicious emails are sent per day;
- 37% of organizations have been victims of ransomware;
- Ransomware encrypted data in 54% of attacks;
- Neutralizing ransomware costs $1.85 million;
- Sodinokibi ransomware made $123 million in profit in 2020;
- 50% of companies do not have an anti-ransomware plan.
Among computer attacks, ransomware is the most dangerous.
The criminal encrypts the victim’s data and demands a ransom to unlock it.
If this is the case for you or your company, the first thing you should know is that the ransom should never be paid.
As a second step, contact a specialized company like HelpRansomware.
He has over 25 years of experience in data recovery, forensics, decryption, and cibersecurity.

Fast & Guaranteed Recovery
HelpRansomware provides a 100% guaranteed ransomware removal and data recovery service, with 24/7 worldwide assistance.



