Are you looking for ransomware solutions to remove cryptographic malware used for cyber extortion? Here is the guide for you.

Fast & Guaranteed Recovery
HelpRansomware provides a 100% guaranteed ransomware removal and data recovery service, with 24/7 worldwide assistance.
Why you need to protect yourself from ransomware
Ransomware is a type of cryptographic malware used for cyber extortion.
The ransomware holds your computer or files hostage via encryption while demanding payment in exchange for the decryption key and the release of access to your device.
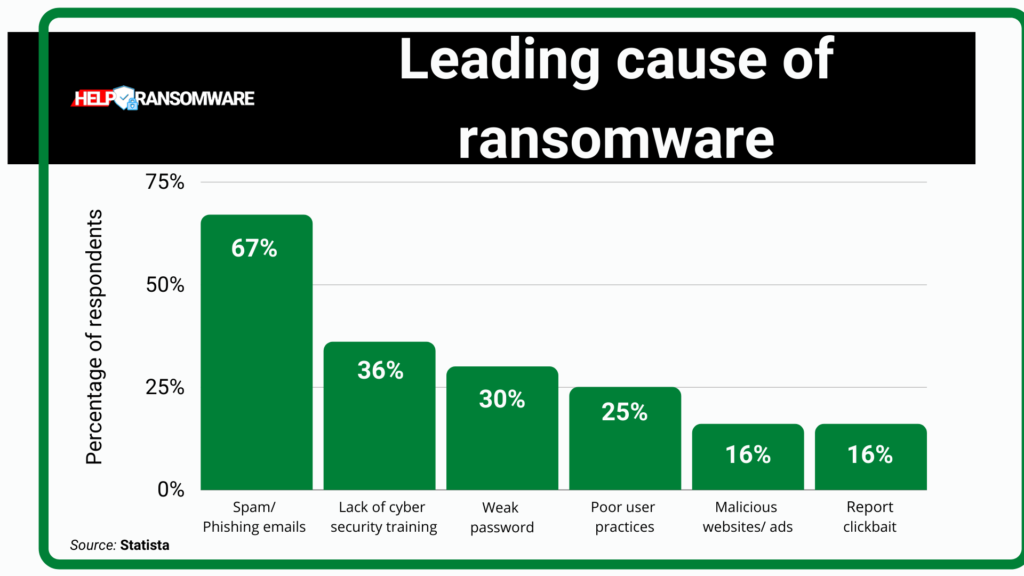
Ransomware spreads via phishing attacks.
These are malicious emails that contain infected attachments or programs or a link to a compromised website.
Ransomware attacks have evolved to target companies and organizations: by encrypting entire computer networks or files and disrupting corporate operations until the person pays the ransom, threatening to make personal data public on the web, a real business developed.
Once a system is infected, the computer is locked and the files encrypted, you will not be able to use your device’s necessary features.
Typically, when you first try to use an infected machine, you see a pop-up window informing you that you need to pay a certain amount of money to reclaim your device and associated data.
Some ransomware programs, or the cybercriminals behind them, impersonate government or police agencies to intimidate victims, claiming that there are security reasons why the computer turned off and insisting on paying the penalty or fine.
As attacks are steadily increasing, businesses and individuals should be more aware of the risks they run and, consequently, know best practices for prevent ransomware attack.

Fast & Guaranteed Recovery
HelpRansomware provides a 100% guaranteed ransomware removal and data recovery service, with 24/7 worldwide assistance.
Ransomware protection tips and best practices
There are several ways that companies and their employees can play a proactive role in protecting the company’s sensitive data from ransomware attacks.
Here are some practical examples.
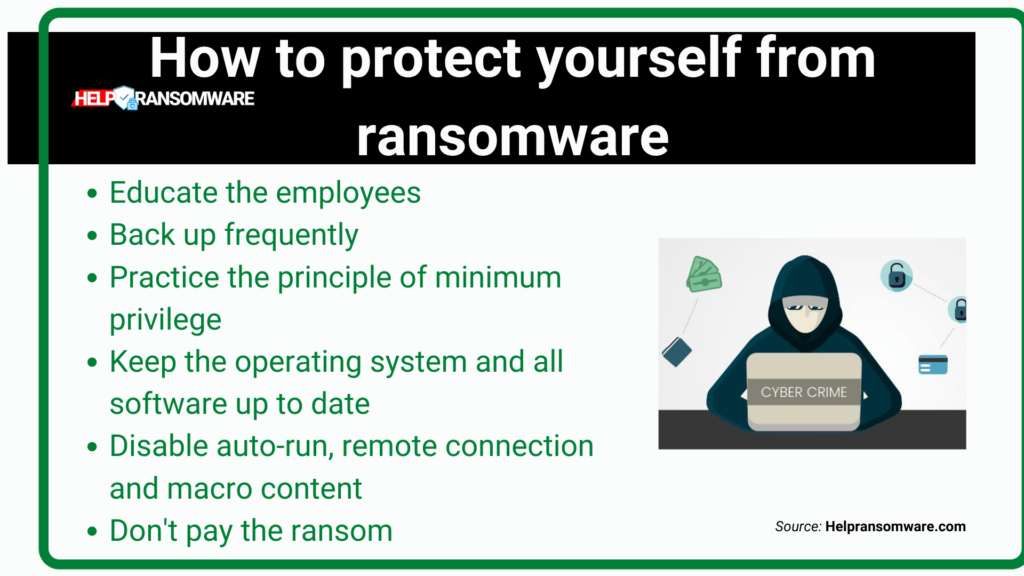
Educate Employees
This is the first line of ransomware prevention. Since ransomware is commonly introduced via email attachments and links, providing employees with the knowledge they need to use email safely can prevent many ransomware attacks.
Train employees on recognizing phishing attacks and best practices: don’t open attachments or links in emails from unknown senders, check link URLs, and never click on pop-up windows – these are little things that can make the difference.
Training should be continuous, don’t save with a single skimpy session! Only then you can be sure that your employees keep up with new threats and maintain safe habits.
Backup files regularly and frequently
Having data backup jobs can significantly limit the damage caused by a ransomware attack, as encrypted data can restore without paying a ransom.
Practice the principle of least privilege: granting unrestricted access to networks and software applications is not only dangerous to the security of the organization. Still, it can also lead to many errors and other setbacks resulting from the use of programs or features to which they do not require access. Set up employee accounts only with the access privileges required by their job roles.
Keep operating systems and all software up-to-date
Software updates typically contain patches to measure security vulnerabilities and should be installed as soon as they become available. Enable automatic updates whenever possible to make this process easier.
Disable features like autorun, remote desktop connections, and macro content in Microsoft Office applications which are components not needed for most employees but can be exploited by attackers to spread ransomware and other malware forms.
Don’t pay the ransom unless necessary – paying the ransom just makes you a target for future attacks and does not guarantee that you will return your data. Unless you have no other choice, avoid paying the ransoms. Contact those who know more than you and have the proper means and knowledge to fight ransomware: contact HelpRansomware and ask for a quote.

Fast & Guaranteed Recovery
HelpRansomware provides a 100% guaranteed ransomware removal and data recovery service, with 24/7 worldwide assistance.
Ransomware: Solutions To Protect Yourself
In addition to following the practices listed above, companies should consider implementing ransomware protection solutions to improve their systems’ defenses against attacks.
Ransomware protection that relies on signature-based security methods is largely ineffective, as new ransomware programs are continually being developed.
Ransomware protection today requires a multi-pronged approach that combines user training with ransomware prevention and detection solutions.
Solutions such as advanced threat protection or endpoint detection and response provide behavior-based detection and blocking of ransomware attacks that go beyond the limits of signature-based detection of known malware.
Additionally, many companies implement application whitelisting to strengthen ransomware protection – this solution allows only certain applications to run, reducing the risk of ransomware programs running on local devices.
Immediate Ransomware Help
Don’t let ransomware hold your business hostage. Our experts are ready to recover your data and secure your systems.