For years, ransomware has been explained as a technical threat: malware, encryption, unauthorized access. However, that explanation falls short when you try to understand why it continues to work so effectively, even in organizations with advanced security measures.
The reality is that ransomware is notable not only for what it does to systems, but also for its impact on people. When a company faces a situation of being locked out, losing access, or facing a direct threat, what changes is not only the infrastructure, but also the way decisions are made.
That’s where the attacker finds his advantage.
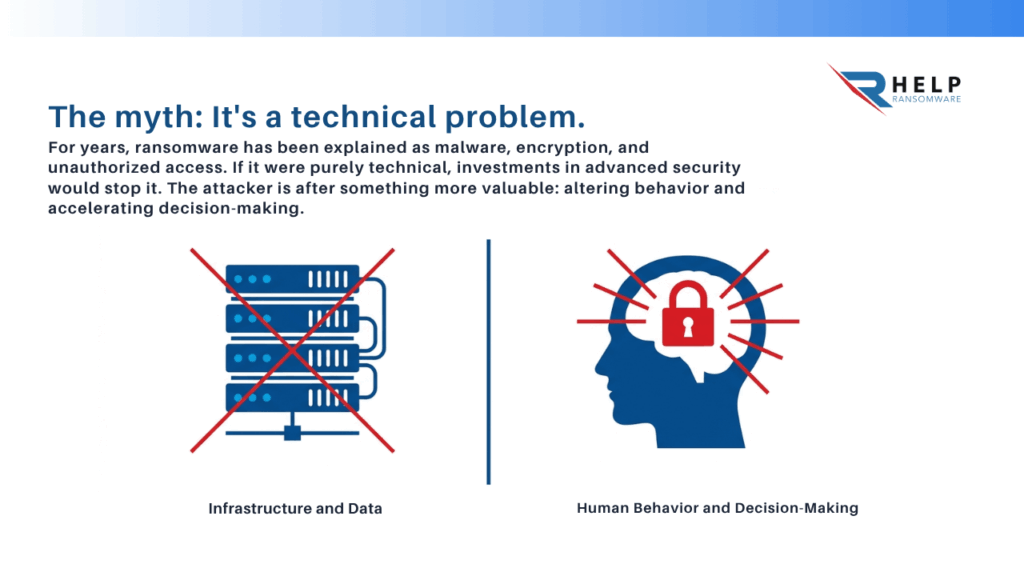
Because ransomware doesn’t need to be technically perfect if it achieves something much more valuable: altering behavior , accelerating decisions , and generating enough pressure for someone to act before analyzing.
The real start of the attack is not the encryption.
One of the most common mistakes is thinking that the attack begins when the locked files or the ransom note appear. At that point, the process is actually already well underway.
Long before that, there has been an initial, usually discreet, access that goes unnoticed. This access typically occurs through everyday actions: opening an email, downloading a file, or interacting with a seemingly legitimate link.
Understanding how to identify a ransomware attack involves precisely looking before the damage is visible, recognizing signs such as changes in system behavior or communications that generate urgency without clear justification.
Psychology as a gateway
Attackers don’t rely solely on technical vulnerabilities. In many cases, the entry point lies in how a person interprets a situation.
INCIBE ‘s analysis of psychology in cybersecurity explains how the most effective attacks combine technical knowledge with an understanding of human behavior .

Expert Ransomware Removal
Our certified professionals have over 25 years of experience in ransomware removal, data recovery, and computer security.
This is especially clear in scenarios such as sextortion and online blackmail, where the attacker builds the entire threat on emotional elements such as fear , shame , or public exposure .
Ransomware shares that same principle: it doesn’t just seek to enter the system, it seeks to provoke a reaction.
Fear: the element that triggers the response
Once the attack becomes visible, the dynamics change. It’s no longer about access, but about control.
The ransomware message is designed to elicit an immediate response. It introduces the possibility of data loss, operational disruption, or reputational damage, creating a sense of risk that overrides rational analysis.
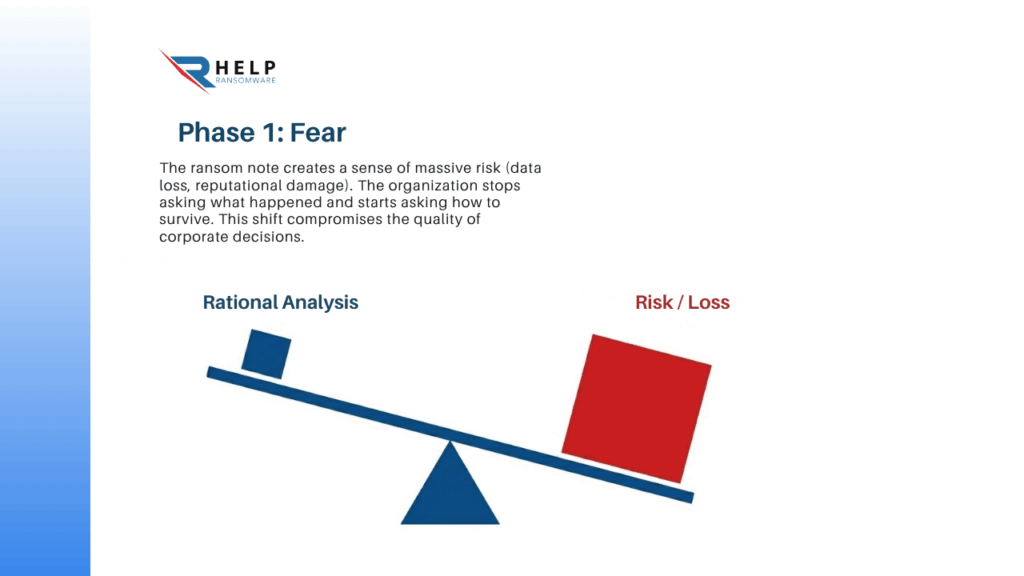
At that point, the organization stops wondering what has happened.
She begins to wonder how to avoid the damage.
That change is key.
Fear not only affects the perception of the problem, it directly affects the quality of decisions.
When reaction replaces analysis
Under pressure, standard processes are no longer applied. The ability to validate information decreases, and the tendency to act quickly increases.
This is where many organizations make critical mistakes, such as trying to resolve the situation immediately without understanding its true scope. For example, acting rashly when trying to remove ransomware can worsen the impact without a complete picture.
The problem is not a lack of information.
It’s excessive urgency.
Urgency: the factor that breaks down processes
If fear triggers a reaction, urgency accelerates it to the point of making it difficult to control.
The attackers introduce deadlines, limits, and escalating consequences. It’s not a technical issue, but a strategy designed to reduce the time available for thinking.
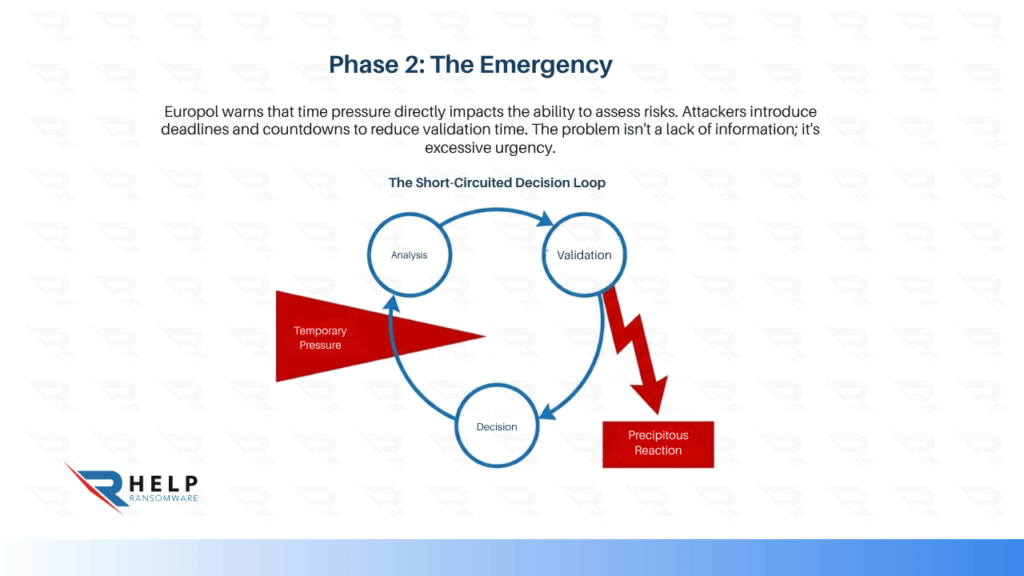
Europol explains this in its guide on mindset towards scams, where it points out how time pressure directly affects the ability to assess risks.
When processes stop working
Under normal conditions, a company follows a clear logic: analysis, validation, decision.
During an attack, that logic breaks down.
Decisions are made with incomplete information, in parallel, and under pressure. This generates inconsistencies, delays, and, in many cases, errors that amplify the impact.
Ransomware doesn’t need to break technology.
It needs to break the way an organization makes decisions.
Chaos: the scenario where the attack consolidates
As the incident progresses, the objective ceases to be technical and becomes organizational.
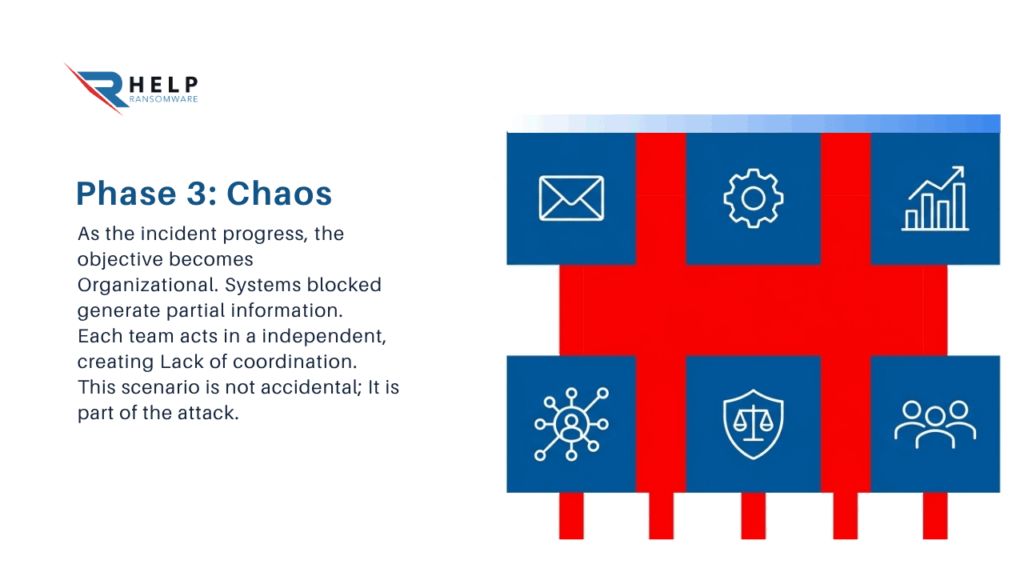
Systems fail, access is blocked, and information stops flowing normally. Each team has a partial view of what’s happening, leading to uncertainty , lack of coordination , and loss of control.
This scenario is not accidental.
It’s part of the attack.
The importance of leadership under pressure
When there is no clear response structure, chaos is amplified. Each area acts independently, without a shared vision.
This is where the role of management becomes crucial. As discussed in CEO and ransomware, the ability to make decisions under pressure largely determines the outcome of the incident.
Ransomware doesn’t just measure technical security.
It measures an organization’s ability to coordinate.
Why it still works even today
Despite investment in tools and technology, ransomware remains an effective threat.
One of the reasons is that it relies on something much more stable than any system: human behavior.
The most dangerous ransomware attacks are not always the most sophisticated, but rather those that best exploit situations of pressure, urgency, or lack of visibility.
Another reason is that many organizations continue to focus their preparation on the technical aspects, without sufficiently addressing the response.
Therefore, initiatives such as cyber training allow training not only in prevention, but also in decision-making in real-life scenarios.
What changes when you understand the psychology of ransomware?
When a company understands that the problem is not just technical, it changes its approach.
Security is no longer solely focused on systems, but now includes people , processes , and decisions.
This allows for a reduction in impulsive reactions, improved coordination, and greater control during the incident.
The risk is not eliminated.
But the impact is reduced.
Ransomware does not only exploit technical vulnerabilities.
Exploit decisions.
At HelpRansomware we work to help you understand how attackers operate , improve decision-making, and reduce the impact when an attack occurs.
Conclusion
Ransomware works because it doesn’t just attack systems.
It acts on emotions , processes , and behavior.
Fear, urgency, and chaos are not side effects. They are elements designed to force quick and irrational decisions.
Organizations that understand this do not eliminate risk, but they are in a better position to manage it.
Frequently Asked Questions (FAQ)

Immediate Ransomware Help
Don’t let ransomware hold your business hostage. Our experts are ready to recover your data and secure your systems.
Is ransomware just a technical problem?
No, it also involves psychological and organizational factors.
Why is it still so effective?
Because it exploits human behavior under pressure.
What is most critical during an attack?
Decision-making under conditions of uncertainty.
Can a company prepare for this?
Yes, by training both the technical and organizational aspects.
Is technology enough?
No, it is also necessary to work on the human response.



