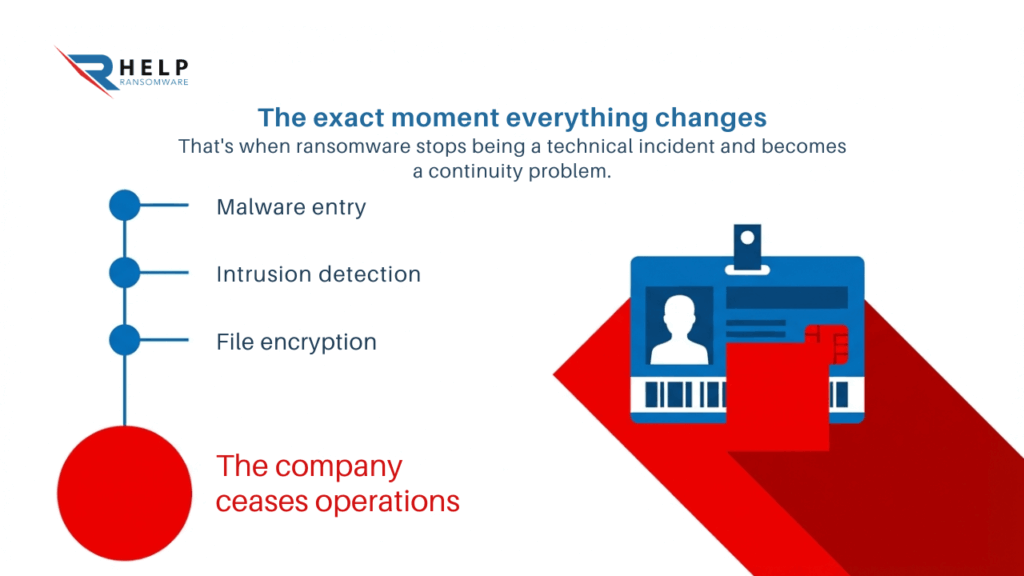
There is a very specific moment in any ransomware attack when everything changes.
It’s not when the malware gets in.
It’s not when the intrusion is detected.
Not even when the files start being encrypted.
That’s when the company stops working.
That moment when someone tries to access a critical system and can’t. When a process stops, an order doesn’t go out, or a decision can’t be made because the data is no longer available.
That’s where ransomware stops being a technical incident and becomes a continuity problem.
And that’s where the awkward question comes in:
Who’s in charge when everything fails?
When technology stops supporting the business
For years, companies have built their operations on increasingly complex digital systems: ERP, CRM, cloud platforms, internal tools. Everything connected, everything interdependent.
The problem is that this efficiency also creates dependency. When an attack hits, it’s not just one system that goes down. The entire operational chain breaks down.
The transition from technical incident to business crisis
In the first few minutes, the focus is on the technical aspects: isolating, analyzing, containing. But that focus doesn’t last long.
Very soon, the organization faces something more uncomfortable: it cannot operate.
At that point, many companies try to react with technical solutions, such as attempting to recover encrypted files. But the reality is that recovering data is not the same as recovering the business.
Because while efforts are underway to restore order, decisions remain blocked, equipment remains idle, and the impact continues to grow.
The false security of digital infrastructure
The most common mistake is thinking that technology sustains the business. In reality, it sustains it while it’s working.
When it stops doing that, all that remains is the organization’s ability to adapt.
Companies affected by ransomware describe it very clearly: the biggest problem wasn’t the encryption, it was not knowing how to proceed.
Ransomware does not destroy systems, it exposes dependencies.
Who takes control in the midst of chaos
When everything comes to a standstill, someone has to decide what to do. And this is where many organizations fail.
The CEO: deciding without complete information
Under normal circumstances, strategic decisions are made with data, analysis, and time. In a ransomware attack, none of that exists.
The CEO must make decisions with partial information, under pressure, and with immediate consequences.
Is all activity halted or is an attempt made to maintain it partially?
Is the incident reported or is it awaited?
Is negotiation being considered?
None of these decisions are technical. They are all business decisions.
Ransomware turns uncertainty into a leadership problem.

Expert Ransomware Removal
Our certified professionals have over 25 years of experience in ransomware removal, data recovery, and computer security.
The technical team: essential, but not enough
The security team is key to understanding what’s happening. They analyze the scope, identify the type of attack, and assess the affected systems.
In some cases, it can even detect patterns associated with specific families, such as different versions of CryptoLocker, helping to anticipate the attacker’s behavior.
But their role is not to decide what to do with the company.
The technical team explains the problem. Management decides how to address it.
The organization: coordination or collapse
A ransomware attack is not an isolated problem. It is a widespread event.
It affects operations, legal, communications, and management. If each area acts separately, the result is disorder, duplication, and delays.
That’s why more and more companies are working with Crisis Management structures designed specifically for these types of scenarios.
Because when there is no coordination, the impact not only increases: it gets out of control.
Organizational chaos multiplies the damage of the attack.
Business continuity: what it really means
Talking about continuity is not talking about recovery. It’s talking about operational survival.
The myth of backups
For years, many companies have relied on backups as the ultimate solution.
But current ransomware doesn’t work that way.
Attackers gain access earlier, move within the network, identify key systems, and in many cases, compromise backups as well.
And even if they don’t, restoration is not immediate.
During that time, the company remains inoperative.
Moving forward is not going back
Business continuity is not about restoring everything that’s been lost. It’s about deciding what’s essential to move forward.
Which processes should be maintained? Which operations can wait? Which customers should be prioritized?
This is where technology gives way to strategy.
Even advanced tools, such as artificial intelligence in cybersecurity, can help anticipate risks, but they do not replace decision-making.
Continuity is a matter of priorities, not systems.
The lasting impact: reputation and trust
When the systems come back online, the problem doesn’t disappear. It just changes form.
The damage that does not appear in the systems
Customers who doubt. Partners who question. Internal teams that lose confidence.
The reputational impact is not immediate, but it is profound.
Many companies only understand the cyber risks and reputational impact later, when they have already lost opportunities or credibility.
Trust takes years to build and minutes to weaken.
A problem recognized at the European level
The European approach to cybersecurity is no longer focused solely on protection, but on resilience.
The ENISA Cybersecurity Market Analysis Framework clearly points to the need to integrate business continuity within the security strategy.
For its part, the CERT-EU CTI Framework reinforces the importance of understanding how attackers operate before they act.
Ransomware is no longer considered an exceptional event, but a structural risk.
What truly differentiates companies
It’s not the technology they have.
It’s how they react when it fails.
Preparation versus improvisation
The companies that manage these incidents best are not those that are never attacked. They are the ones that have worked beforehand on how to respond.
They have defined roles. They have established processes. They have practiced scenarios.
They know who decides and when.
When the attack occurs, they don’t start from scratch.

Expert Ransomware Removal
Our certified professionals have over 25 years of experience in ransomware removal, data recovery, and computer security.
Leadership versus gridlock
In a crisis, time is the most critical resource.
Organizations that hesitate lose room to maneuver. Those that act with clarity, even with incomplete information, better control the impact.
Ransomware doesn’t just test security. It tests leadership.
When everything works, continuity is not questioned.
When everything fails, it’s too late to define it.
At HelpRansomware we work to strengthen your responsiveness and business continuity, helping your organization make critical decisions before you have to do so under pressure.
Conclusion
Ransomware is not a technical problem that can be solved with tools.
It is a real test of how an organization functions when it loses control.
When systems fail, all that remains is the ability to decide, coordinate, and prioritize.
Companies that understand this don’t just survive.
They emerge stronger.
Frequently Asked Questions (FAQ)
Who should lead during a ransomware attack?
The company management, with the support of the technical team.
Is having backups enough?
No. They help with recovery, but they don’t guarantee continuity.
Why does the response fail in many companies?
Due to a lack of coordination and clear leadership.
Can business continuity be trained?
Yes, through simulations and prior planning.
What is the most critical factor in an attack?
Speed and clarity in decision-making.



