Have you been infected with ransomware? Here are the top 150 free tools to ransomware decryption without paying ransom.

Fast & Guaranteed Recovery
HelpRansomware provides a 100% guaranteed ransomware removal and data recovery service, with 24/7 worldwide assistance.
Fundamental premise: in a thorny case like the ransomware threat’s one, do-it-yourself ransomware solutions involve a large percentage of risk.
To have greater certainty in recovering your data and ensure greater future security, it is always better to contact specialists: HelpRansomware uses experts’ knowledge and the most advanced technologies to help you.
How to recover data
If your network is infected with ransomware, you can follow the steps below to recover essential data:
- Don’t pay the ransom because there is no guarantee that the ransomware creators will give you access to your data.
- Find all available backups and consider keeping data backups in safe and offline locations.
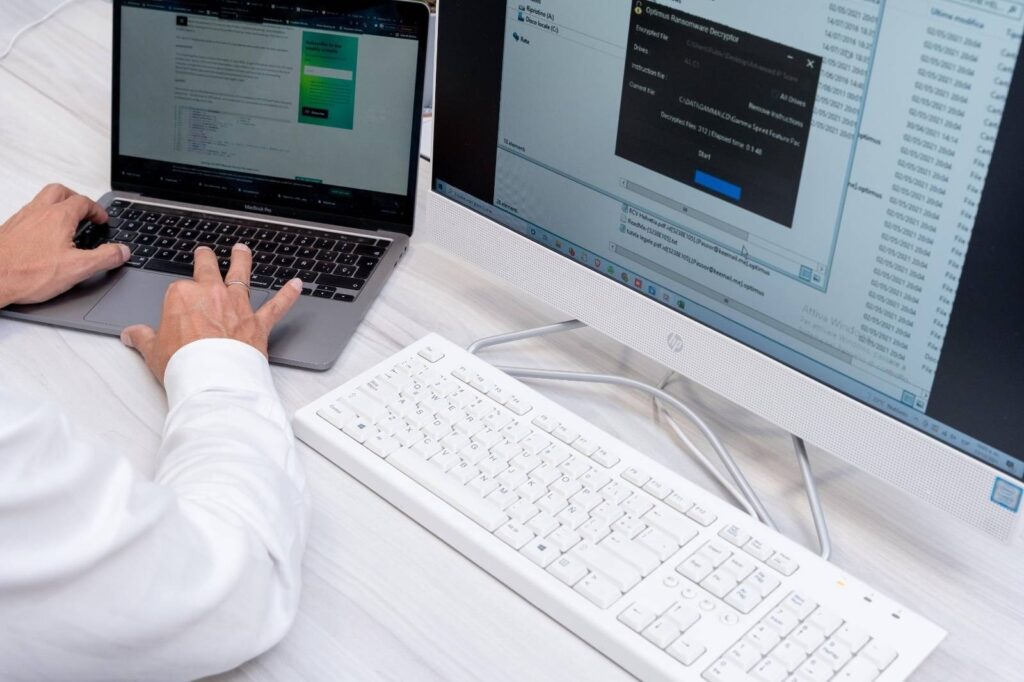
- If there are no backups, you should try to decrypt the data locked by the ransomware using the best ransomware decryption tools available.
In this anti-ransomware guide, we have included free decryption tools that you can use to avoid all types of malware and remove ransomware.
How to identify the ransomware you are infected with
The ransom note often gives details about the type of ransomware with which the files were encrypted, but it may happen that you do not have this information at hand.
Repeatedly readers ask us to show which encryption extensions belong to which ransomware families, but many extensions mark new types of encrypted ransomware for which no decryptors are available.
If you need help identifying what type of ransomware is infecting your system, you can use these two tools:
- Crypto Sheriff by No More ransomware;
- ID Ransomware by Malwarehunter Team.
Ransomware decryption tools – an ever-updating list
Disclaimer: the following list is not complete and probably will never be because malware and ransomware are constantly evolving.
So use it, but also do a documented research: secure data decryption can be a nerve-wracking and lengthy process, contacting specialists like the HelpRansomware team is the best solution, always.
We will do our best to keep this list up to date and add other tools to it.
Contributions and suggestions are more than welcome, as we are committed to following them promptly and including them on the list.
Some of the ransomware decryption tools mentioned below are easy to use, while others require a little more technical knowledge.
Immediate Ransomware Help
Don’t let ransomware hold your business hostage. Our experts are ready to recover your data and secure your systems.
- .777 ransomware decrypting tool
- 7even-HONE$T decrypting tool
- .8lock8 ransomware decrypting tool + explanations
- 7ev3n decrypting tool
- AES_NI Rakhni Decryptor tool
- Agent.iih decrypting tool (decrypted by the Rakhni Decryptor)
- Alcatraz Ransom decryptor tool
- Alma decrypting tool
- Al-Namrood decrypting tool
- Alpha decrypting tool
- AlphaLocker decrypting tool
- Amnesia Ransom decryptor tool
- Amnesia Ransom 2 decryptor tool
- Apocalypse decrypting tool
- ApocalypseVM decrypting tool + alternative
- Aura decrypting tool (decrypted by the Rakhni Decryptor)
- AutoIT decrypting tool (decrypted by the Rannoh Decryptor)
- AutoLT decrypting tool (decrypted by the Rannoh Decryptor)
- Autolocky decrypting tool
- Badblock decrypting tool + alternative 1
- BarRax Ransom decryption tool
- Bart decrypting tool
- BigBobRoss decrypting tool
- BitCryptor decrypting tool
- BitStak decrypting tool
- BTCWare Ransom decryptor
- Cerber decryption tool
- Chimera decrypting tool + alternative 1 + alternative 2
- CoinVault decrypting tool
- Cry128 decrypting tool
- Cry9 Ransom decrypting tool
- Cryakl decrypting tool (decrypted by the Rannoh Decryptor)
- Crybola decrypting tool (decrypted by the Rannoh Decryptor)
- CrypBoss decrypting tool
- Crypren decrypting tool
- Crypt38 decrypting tool
- Crypt888 (see also Mircop) decrypting tool
- CryptInfinite decrypting tool
- CryptoDefense decrypting tool
- CryptFile2 decrypting tool (decrypted by the CryptoMix Decryptor)
- CryptoHost (a.k.a. Manamecrypt) decrypting tool
- Cryptokluchen decrypting tool (decrypted by the Rakhni Decryptor)
- CryptoMix Ransom decrypting tool + offline alternative
- CryptON decryption tool
- CryptoTorLocker decrypting tool
- CryptXXX decrypting tool
- CrySIS decrypting tool (decrypted by the Rakhni Decryptor – additional details)
- CTB-Locker Web decrypting tool
- CuteRansomware decrypting tool (decrypted by the my-Little-Ransomware Decryptor)
- Damage ransom decrypting tool
- DemoTool decrypting tool
- Dharma Ransom Rakhni decryptor tool
- DeCrypt Protect decrypting tool
- Democry decrypting tool (decrypted by the Rakhni Decryptor)
- Derialock ransom decryptor tool
- Dharma Decryptor
- DMA Locker decrypting tool + DMA2 Locker decoding tool
- Fabiansomware decrypting tool
- Everbe Ransomware decrypting tool
- Encryptile decrypting tool
- FenixLocker – decrypting tool
- FilesLocker decrypting tool
- FindZip decrypting tool
- FortuneCrypt decrypting tool (decrypted by the Rakhni Decryptor)
- Fury decrypting tool (decrypted by the Rannoh Decryptor)
- GhostCrypt decrypting tool
- Globe / Purge decrypting tool + alternative
- Globe3 decryption tool
- Gomasom decrypting tool
- GandCrab decrypting tool
- Hacked decrypting tool
- Hakbit decryptor
- Harasom decrypting tool
- HydraCrypt decrypting tool
- HiddenTear decrypting tool
- Jaff decrypter tool
- Jigsaw/CryptoHit decrypting tool + alternative
- KeRanger decrypting tool
- KeyBTC decrypting tool
- KimcilWare decrypting tool
- Lamer decrypting tool (decrypted by the Rakhni Decryptor)
- LambdaLocker decryption tool
- LeChiffre decrypting tool+alternative
- Legion decrypting tool
- Linux.Encoder decrypting tool
- Lobzik decrypting tool (decrypted by the Rakhni Decryptor)
- Lock Screen ransomware decrypting tool
- Locker decrypting tool
- Lortok decrypting tool (decrypted by the Rakhni Decryptor)
- MacRansom decrypting tool
- Marlboro ransom decryption tool
- MarsJoke decryption tool
- Manamecrypt decrypting tool (a.k.a. CryptoHost)
- Mircop decrypting tool + alternative
- Merry Christmas / MRCR decryptor
- Mole decryptor tool
- MoneroPay Ransomware decrypting tool
- my-Little-Ransomware decrypting tool
- Nanolocker decrypting tool
- Nemucod decrypting tool + alternative
- NMoreira ransomware decryption tool
- Noobcrypt decryption tool
- ODCODC decrypting tool
- OpenToYou decryption tools
- Operation Global III Ransomware decrypting tool
- Ozozalocker ransomware decryptor
- Paradise ransomware decryptor
- PClock decrypting tool
- Petya decrypting tool + alternative
- Philadelphia decrypting tool
- PizzaCrypts decrypting tool
- Planetary ransomware decrypting tool
- Pletor decrypting tool (decrypted by the Rakhni Decryptor)
- Polyglot decrypting tool (decrypted by the Rannoh Decryptor)
- Pompous decrypting tool
- PowerWare / PoshCoder decrypting tool
- Popcorn Ransom decrypting tool
- PyLocky Ransomware decrypting tool
- Radamant decrypting tool
- Rakhni decrypting tool
- Rannoh decrypting tool
- Rector decrypting tool
- Rotor decrypting tool (decrypted by the Rakhni Decryptor)
- Scraper decrypting tool
- Shade / Troldesh decrypting tool + alternative
- SNSLocker decrypting tool
- Stampado decrypting tool + alternative
- STOP Djvu Ransomware decryptor
- SZFlocker decrypting tool
- Teamxrat / Xpan decryption tool
- TeleCrypt decrypting tool (additional details)
- TeslaCrypt decrypting tool + alternative 1 + alternative 2
- Thanatos decryption tool
- TorrentLocker decrypting tool
- Umbrecrypt decrypting tool
- Wildfire decrypting tool + alternative
- WannaCry decryption tool + Guide
- XData Ransom decryption tool
- XORBAT decrypting tool
- XORIST decrypting tool + alternative
- Yatron decrypting tool(decrypted by the Rakhni Decryptor)
- Zeta decrypting tool (decrypted by the CryptoMix Decryptor)
Explanation of ransomware families and decryption tools
As you may have noticed, some of these decryption tools work for multiple ransomware families, while some families have more than one solution (rarer).
From a practical point of view, some of the decryptors are easy to use, but some require technical know-how.
As much as we would like this process to be easier, it is not always possible to make it so.
Fast & Guaranteed Recovery
HelpRansomware provides a 100% guaranteed ransomware removal and data recovery service, with 24/7 worldwide assistance.
No matter how much work and time researchers put into reverse engineering cryptoware, the truth is that we will never have a solution to all of these infections.
It would take an army of cybersecurity specialists working around the clock to achieve something like this.
How to avoid ransomware
One of the most effective ways to prevent ransomware from wreaking havoc and blocking your sensitive data is to stay alert and be proactive.
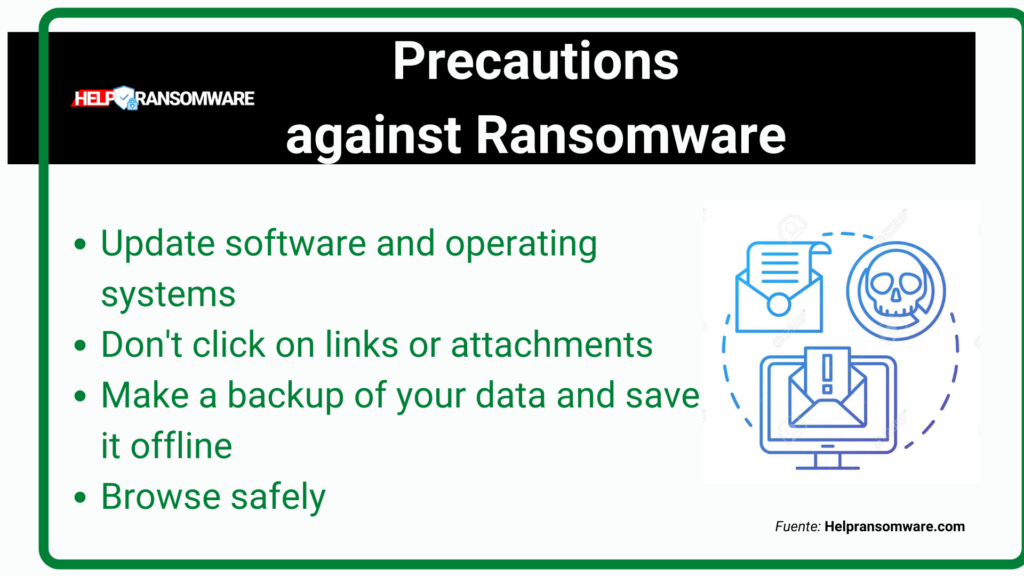
An excellent idea is to securely keep offline copies of vital information and equip your company with cyber-insurance.
That way, even if cybercriminals gain access to your computers and infect them with malware, you can wipe the system and restore your latest backup.
You will not lose money and no critical information will be compromised!
So please don’t postpone the backup process of your data.
Do it now and get safe!
Also, make your employees aware of this and share the basics of proactive protection with them; doing so will limit the risk of them becoming victims of ransomware and, consequently, you will also better protect your corporate network.
With the emergence of new ransomware, researchers decrypt some types, but others evolve into new variants and end up creating anything but a cat and mouse game.
Therefore, proactivity is vital.
Paying the ransom never guarantees that your data will actually be returned, as criminals could still put it up for sale on the Dark Web.
Therefore, prevention remains the best medicine as always.
However, the best doctors remain the experts: don’t make the mistake of thinking you can always solve everything yourself, contact HelpRansomware.

Expert Ransomware Removal
Our certified professionals have over 25 years of experience in ransomware removal, data recovery, and computer security.



