What Does WannaCry Ransomware Do And Encrypt? How much damage did WannaCry cause, and which sectors were most affected?
Fast & Guaranteed Recovery
HelpRansomware provides a 100% guaranteed ransomware removal and data recovery service, with 24/7 worldwide assistance.
What is WannaCry Ransomware?
WannaCry is a ransomware that hackers use to extort money from users in exchange for recovering encrypted files.
It is undoubtedly one of the most famous strains globally.
What type of malware is WannaCry ransomware?
WannaCry is a type of malware that blocks data on a computer and demands a ransom to decrypt ransomware files.
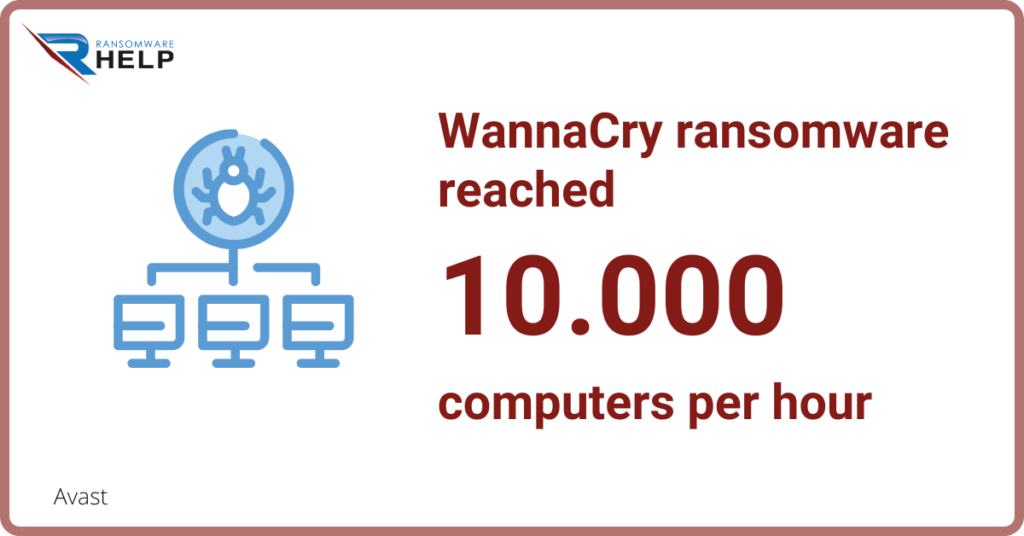
It is one of the most significant cyber attacks in history, perpetrated in May 2017.Avast observed that the WannaCry ransomwarereached 10,000 computers per hour.
Is WannaCry a virus or a worm?
It is not a virus because it does not replicate but a worm because it spreads through networks infecting other computers.
How was WannaCry detected?
Marcus Hutchins, a 22-year-old British cybersecurity expert, detected the WannaCry ransomware attack while analyzing a new variant of the Petya ransomware.
On May 12, 2017, he registered a domain for the malware shutdown switch and created a Bitcoin address for donations.
The FBI arrested him and charged him with attempting to cause damage to protected computers.
Who was behind the WannaCry ransomware?
It is still unclear who was behind the WannaCry ransomware attack, but some clues are pointing to North Korea.
What does WannaCry ransomware do?
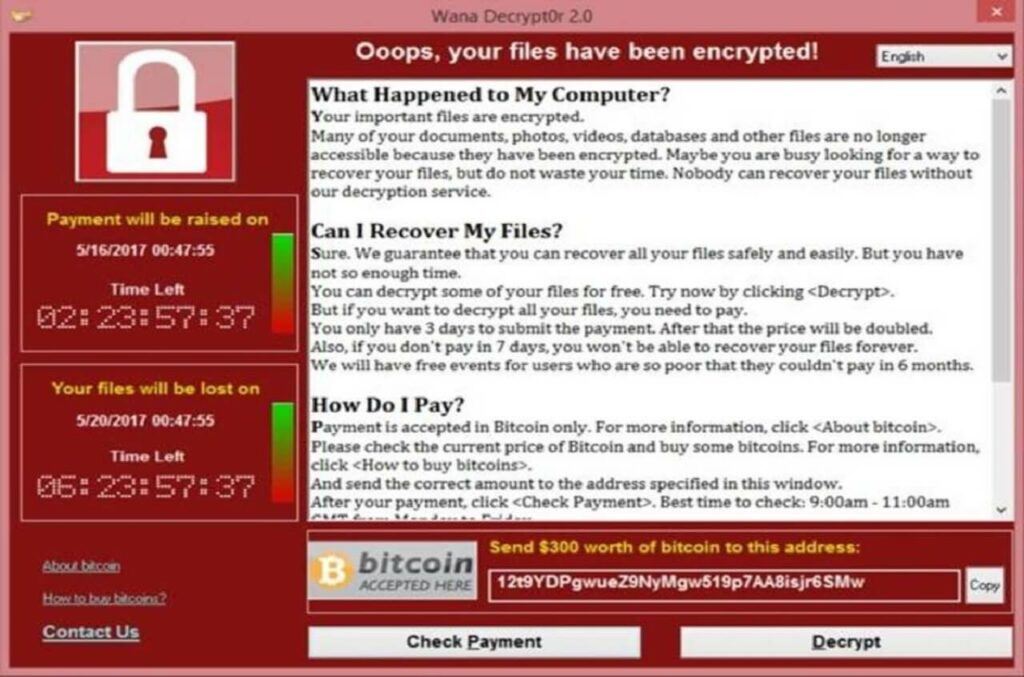
The WannaCry ransomware aim is to encrypt infected computers and ask for a ransom to open encrypted files.
Ransomware blocks data by adding the extension WNCRY and then spreads over the network by exploiting a vulnerability in Windows XP.
It also installs a service called ‘@WanaDecryptor’.
It then runs every five minutes and scans all available networks to detect other vulnerable computers running outdated versions of the Windows operating system.
If it finds any, it also infects them. The malware displays a warning to inform the victims that their files have been encrypted and asks them to pay the ransom.
What strings does WannaCry use to encrypt files?
The ransomware uses a combination of two strings to perform encryption: “@Please_read@” and “@wannacry@“.
What is the EternalBlue vulnerability?
The CISA (Cybersecurity and Infrastructure Security Agency) explains what EternalBlue is and how it attacks system vulnerabilities:
“EternalBlue is an exploit that allows cyber threat actors to remotely execute arbitrary code and gain access to a network by sending specially crafted packets. It exploits a software vulnerability in Microsoft‘s Windows operating systems (OS) Server Message Block (SMB) version 1 (SMBv1) protocol, a network file sharing protocol that allows access to files on a remote server”.

Immediate Ransomware Help
Don’t let ransomware hold your business hostage. Our experts are ready to recover your data and secure your systems.
Which port does WannaCry use?
The National Cyber Securityl Center reports which port this type of ransomware uses:
“As SMBv1 is a vector by which the malware spreads, this can be disabled to prevent further infection if specific systems within an organisation become affected. […] If the above is not possible, you may be able to block SMBv1 ports on network devices and host-based firewalls on workstations. These ports are: UDP: 137 and 138; TCP 139 and 445.”
WannaCry Ransomware Attack
The WannaCry ransomware global cyber attack began on 12 May 2017.
The EternalBlue tool, probably developed by the US National Security Agency and leaked by hackers, originated the attack.
This malware reached more than 150 countries and is one of the most significant cyber attacks in recent history.
Businesses and Governments lost billions of dollars since this malware attack strongly damaged the technology industry.
How much money did WannaCry ask for ransom?
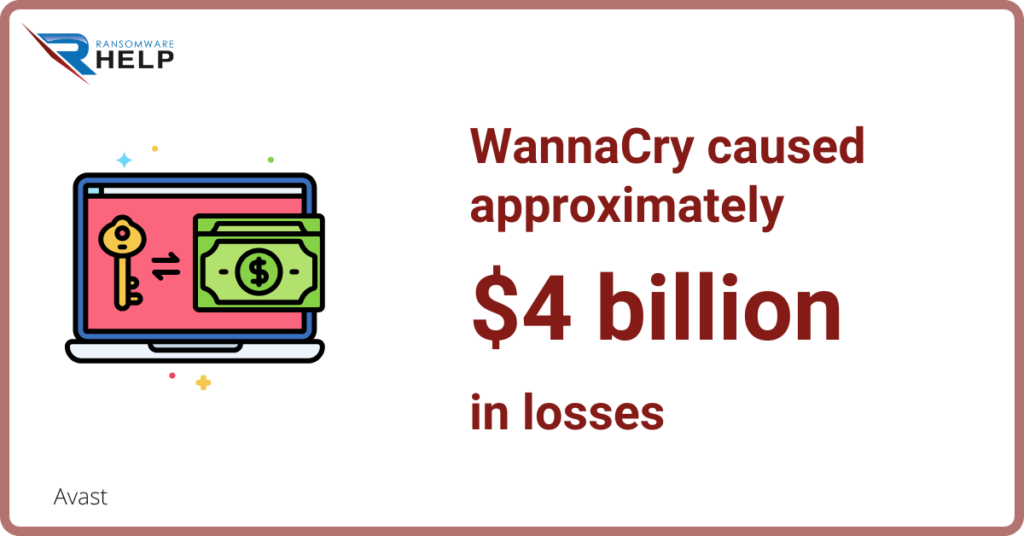
It is not easy to calculate how much money WannaCry earned. However, it caused approximately $4 billion in losses.
Who stopped WannaCry?
A young security researcher from England, Marcus Hutchins, discovered a shutdown switch for the WannaCry ransomware that prevented it from spreading further.
He revealed that registering a hidden domain name in malware code could effectively stop any future Wannacry attack and ransomware encryption.
Which sectors were most affected by WannaCry?
Healthcare and telecommunications industries were most affected by this attack.
The healthcare industry was seriously affected since medical operations are strictly related to operating systems.
Ransomware blocked internal files with a significant impact on their daily operations.
Hospitals and surgeries had to cancel their appointments since they could no longer access calendars, patient records, or even their devices.
The telecommunications industry, which mainly depends on IT infrastructures, was also severely affected by this attack.
Including customer support services, call center operations, data storage, or billing.
How many computers were affected by WannaCry?
Kaspersky argues that the malware attack hit more than 200,000 computers in 150 countries.
How much damage did WannaCry cause?
We can summarize the effects of the WannaCry ransomware attack as follow£:
- 10,000 reached computers per hour;
- More than 150 countries hit;
- Around $4 billion in losses;
- 200,000 computers reached;
- The NHS alone lost $92 million.
WannaCry took advantage of the vulnerability of millions of users through a Windows crash.
How did NHS recover from WannaCry?
The company Kaspersky summarizes the damage suffered by thousands of hospitals and clinics of the UK National Health Service (NHS) after the WannaCry ransomware attack:
“A third of NHS hospital trusts were affected by the attack. Terrifyingly ambulances were reportedly rerouted, leaving people in need of urgent care in need. It was estimated to cost the NHS a whopping £92 million after 19,000 appointments were canceled as a result of the attack.”
How did WannaCry spread?
According to Kaspersky, it spread through Windows retaining the users’ files and requesting the ransom in bitcoins.
What does WannaCry encrypt?
WannaCry attacks computers running Microsoft Windows.
Subsequently, the malware spreads to all email addresses in your contact list on your computer.
It encrypts files with .doc, .jpg, .png, extensions.7z and more.
Is WannaCry ransomware still active?
WannaCry ransomware was active in the past. It was one of the most successful ransomware attacks in history.
WannaCry focused on unpatched Microsoft Windows operating systems and took advantage of a known exploit that the company had not yet patched.
Is WannaCry still a threat?
Ransomware threats are so powerful that it is impossible to rule them out completely.
Malware is constantly evolving, while cybercriminals are growing by the day.
Like all ransomware, WannaCry can be removed and decrypted.
On the one hand, many software are able to remove ransomware.
While decrypting is more complicated. To do this, you must contact a specialized company.
HelpRansomware is an expert in ransomware removal, cybersecurity, and decryption.

Expert Ransomware Removal
Our certified professionals have over 25 years of experience in ransomware removal, data recovery, and computer security.
It ensures the removal of malware and can restore encrypted files.
What happens if you do not pay the ransom to WannaCry?
The main objective of the offenders is to extort the victim with a ransom payment.
No matter if you do not pay the ransom since you can contact a company that specializes in decryption.
The most important thing is to avoid paying and take legal action.
Paying can incentivize hackers to perpetrate other types of cybercrime.
What if you pay WannaCry?
Cybercriminals will not restore the encrypted files and will ask you to pay more.
They take advantage of desperate victims who are ready to pay to get their data back.
Conclusions
This text helps you discover what the WannaCry ransomware can do and encrypt, how much damage it caused, and which sectors were most affected.
We can draw the following conclusions from this article:
- WannaCry is a type of ransomware that cybercriminals use to extort money from victims;
- It is considered one of the most dangerous ransomware attacks in history, which occurred in May 2017;
- It affected 150 countries with a loss of $4 billion for companies and Governments;
- Healthcare and telecommunications were the most affected industries;
- The attack caused the cancellation of 19,000 medical appointments.
Ransomware is extremely dangerous, crippling networks and causing catastrophic damage to infrastructure.
The attack encrypts and deletes all data until the goal – to get money – is achieved.
Specialists insist on not paying the ransom and go to a ransomware removal and decryption company.
HelpRansomware has over 25 years of experience in cybersecurity, malware removal, and decryption.
Immediate Ransomware Help
Don’t let ransomware hold your business hostage. Our experts are ready to recover your data and secure your systems.



