Discover this new guide on how to protect yourself from ransomware on Mac and Windows operating systems [GUIDE 2022].
Immediate Ransomware Help
Don’t let ransomware hold your business hostage. Our experts are ready to recover your data and secure your systems.
What is ransomware
Ransomware is a type of malware that limits access to operating system files.
The cybercriminal demands an economic ransom so that the user or company can reaccess the data.
Kaspersky defines ransomware as follows:
“Ransomware poses a threat to you and your device. The word “ransom” tells you everything you need to know about this pest.”
On many occasions, ransomware shows up because of users’ ignorance of computer security:
- Opening deceptive emails;
- Obsolete hardware and software;
- Visiting suspicious fake websites;
- Refusal to allocate financial resources to computer security.
Who does the ransomware attack?
Ransomware attacks individuals and businesses of all sizes.
From small businesses, large corporations to government headquarters.
A survey conducted of 820 companies by Hornet Security has extracted the following data on the victims of ransomware, divided by the size of the companies.
The figures are as follows:
- Ransomware attacks 18.7% of companies, comprised of 1 to 50 employees;
- 21.3% corresponds to companies with 51 to 200 workers;
- This malware occurs in 25.3% of companies with up 201 to 500 employees;
- 22% to companies, from 501 to 1,000 members;
- Corporations with more than 1,000 employees are attacked on a percentage of 22.7%.
Ransomware and all its types have become a challenge for security teams worldwide.
Ransomware features
Before delving into how to protect yourself from ransomware, let’s get to know its features:
- Encrypts the victim’s files;
- Demand a ransom, in exchange for recovering the data;
- The attacked user receives instructions to obtain the key and restore the encrypted files;
- The economic figure ranges from hundreds to thousands of dollars;
- Currently, Bitcoin is the payment method demanded by cybercriminals because it is not traceable;
- Although there are different types of ransomware, they all have the same goal: to make money;
- It threatens corporations and individuals with publishing private data.

Fast & Guaranteed Recovery
HelpRansomware provides a 100% guaranteed ransomware removal and data recovery service, with 24/7 worldwide assistance.
How a ransomware attacks
The cybercriminal takes control of the infected computer and hijacks the user’s information, encrypting it to remain unreadable if the decryption password is not available.
Extorts the user asking for a financial ransom in exchange for this password so that, supposedly, he can recover his data.
The system’s security is based on the difficulty of factoring in large numbers.
Its operation consists in sending an encrypted message using the recipient’s public key.
Once the encrypted message arrives, they are in charge of decrypting it with their private key.
A widespread attack is phishing: cybercriminals attach a document or link in an email and trick the user into downloading and installing the malware.
Another typical attack is the Trojan, which presents itself as legitimate software, and subsequently infects users.
File encryption
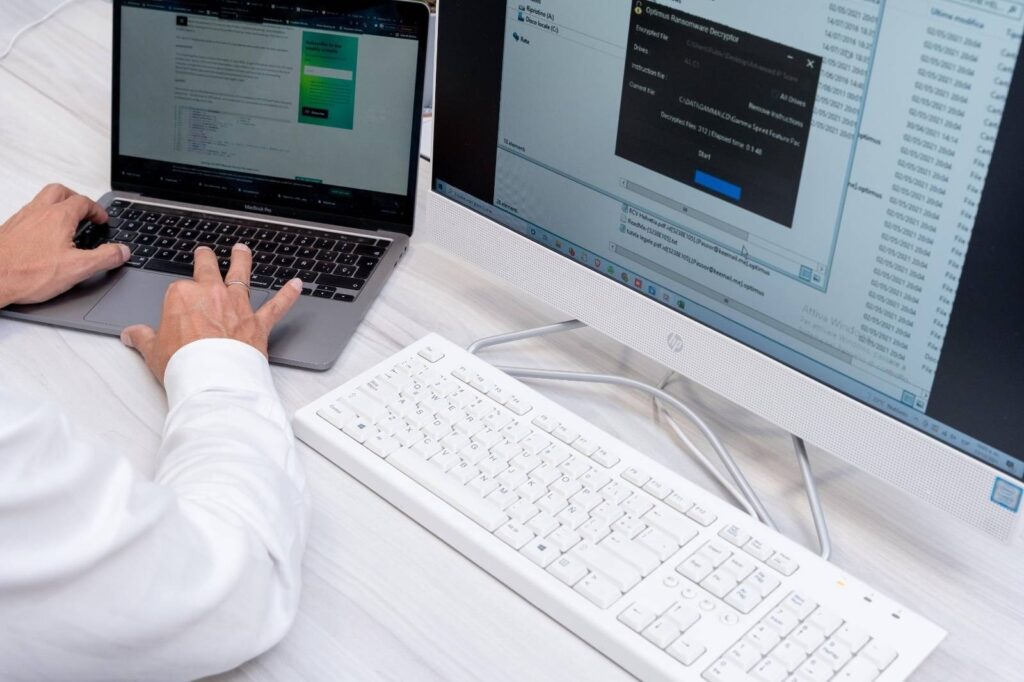
File encryption occurs quickly and unexpectedly.
The ransomware takes control of the device in seconds and looks for the files, encryption target.
Once the computer is encrypted, the malware infects any other hard drive, network devices, USB, and everything connected.
A notice similar to the following appears on the device screen within minutes.
It indicates that all files on the computer are infected.
Likewise, it indicates some instructions, the amount of money, and the time to pay.
The same message is already cyber extortion because the criminal warns that the figure will increase if not paid in the indicated time.
How to protect yourself from ransomware on Windows and Mac
We have already delved into the term ransomware and how it works.
In the following sections, we discover how to protect yourself from ransomware on Windows and Mac.
Protect yourself from ransomware in Windows
The main target of the ransomware attack is the Windows system.
The easiest and most accessible option to protect yourself from ransomware in Windows is the following:
Immediate Ransomware Help
Don’t let ransomware hold your business hostage. Our experts are ready to recover your data and secure your systems.
- Click on “Start”;
- Press “Settings”;
- Click on “Update and security”;
- Then click on “Windows Security”;
- Click on “Viruses and threats protection”;
- You will be able to view current threats, history, and examination;
- You can also click on “Manage ransomware protection”;
- On this screen, the option “Controlled folder access” is disabled by default;
- When activated, Windows requests permissions, and the user must accept them.
This protects your device’s files, folders, and memory areas to prevent unauthorized changes by malicious applications.
Windows Support offers tips to protect yourself from ransomware:
- Update the latest version of Windows;
- Get ransomware detection and recovery using Microsoft 365 advanced protection;
- Make a backup copy of the files;
- Store important files in Microsoft OneDrive;
- Use a modern browser;
- Restart the computer periodically: at least once a week to ensure that the operating system and applications are up to date.
Protect yourself from ransomware on Mac
Today, some users think that ransomware does not attack Mac and iOS.
Although the probability with Windows is higher, ransomware attacks also occur on Macs.
The powerful protection that Apple’s operating system has requires a special effort to infiltrate cybercriminals.
The most problematic types of ransomware are KeRanger and MacRansom.
Likewise, hackers also act against Apple’s browser, Safari.
The best-known method is the FBI/MoneyPak virus, which requests payment in exchange for unlocking.
The macOS user manual also refers to the protection of malicious software:
“You can reduce this risk by using software only from reliable sources.”
To prevent a ransomware attack on Mac, do the following:
- Enter the Apple menu;
- Click “System Preference”;
- Click on “Security and privacy”;
- In “Allow applications downloaded from” there are the sources from which the software is installed.
The safest options are “App Store”, and “App Store and identified developers”.
And, of these two, the best is the first alternative.
We have already explained the options to protect yourself from ransomware, both on Windows and Mac.
But, if you have been the victim of an attack, you should contact a specialized team, such as HelpRansomware.
Our experts recover files from any ransomware safely and quickly.
We know the value of information, understand the situation of a cyberattack, and implement strategies to recover encrypted files.
Immediate Ransomware Help
Don’t let ransomware hold your business hostage. Our experts are ready to recover your data and secure your systems.
Tips to protect yourself from ransomware
Ransomware harms individuals and businesses, encrypting what is most valuable: data.
Below, the HelpRansomware team offers tips to protect yourself from ransomware.
Update the software and operating system
An affordable way to protect yourself from ransomware is to integrate endpoint security.
Thus, you will reduce the entry of ransomware to a device.
It also allows you to analyze when systems have been compromised and ensure that installed security updates.
Remember that updating the operating system and software does not guarantee 100% security.
Why? Cybercriminals work every day to improve and update their attacks.
Email security
Email security is vital to protecting yourself from ransomware.
You should know that the email scanning filter communications, identify threats and block delivery to users.
Thus, the message recipient avoids installing the link generated through phishing.
A posteriori, there are artificial intelligence algorithms, which warn the user of questionable content.
Backups
Backups reduce data loss and are therefore essential for protection.
The information is in multiple locations, such as primary storage, local drives, hard drives, USB, or the cloud.
Browse safely
DNS filtering prevents users from visiting dangerous web pages to download ransomware.
They also block Trojans, which hide legitimate software and malicious advertisements.
On the other hand, site isolation also prevents threats and allows users to navigate quickly and safely.
Not pay the ransom
It is important to emphasize that you do not have to pay the ransom to recover the encrypted files.
Hornet Security survey indicates that one in ten companies (9.2%) had to pay the ransom after ransomware attacks.
But payment is not the solution because it does not ensure that the cybercriminal decrypts the data.
The FBI warns of this on its website:
“The FBI does not support paying a ransom in response to a ransomware attack“
Paying a ransom doesn’t guarantee you or your organization will get any data back.
It also encourages perpetrators to target more victims and offers an incentive for others to get involved in this type of illegal activity.”
Contact an expert team
Reporting the attack to a team of professionals is the best option to recover encrypted data.
The extensive experience of HelpRansomware in the cybersecurity market positions us as the first company in security and digital protection for companies and digital entities.
Our data decryption service has high technology and qualified experts.
Conclusions
This guide has discovered how to protect yourself from ransomware on Mac and Windows operating systems.
From this text, we can draw the following conclusions:
- Sometimes, ransomware shows up because of users’ ignorance of computer security;
- Ransomware attacks individuals and businesses;
- According to a survey by Hornet Security, one in five companies has suffered a ransomware attack;
- File encryption occurs quickly and unexpectedly;
The Windows operating system suffers more episodes than the Mac.

Expert Ransomware Removal
Our certified professionals have over 25 years of experience in ransomware removal, data recovery, and computer security.




