With the new HelpRansomware guide, you will find out what cybercrime is, the most common types, and its effects on cybersecurity.
Immediate Ransomware Help
Don’t let ransomware hold your business hostage. Our experts are ready to recover your data and secure your systems.
What is cybercrime?
Cybercrime is an act perpetrated on the Internet, punishable by law.
Attacks on a computer system, such as ransomware, are considered a cybercrime.
According to the Cambridge Dictionary, the commonly used term cybercrime is a:
“Crime or illegal activity that is done using the internet:”
What are the most common cyber-attacks?
As stated on the Cyber Security Breaches Survey 2021, the major cyber threats are:
- Phishing attacks;
- Others impersonating organizations in email or online;
- Viruses, spyware, or malware;
- Denial of service attacks;
- Hacking of online banks accounts;
- Takeovers of accounts;
- Ransomware;
- Unauthorized accessing of files;
- Others.
Cyber threats: phishing
Phishing is a practical, easy, and inexpensive way for cybercriminals to access users’ confidential information.
This cybercrime occurs by sending a fraudulent email or other similar media hoping that the user will “bite”.
Victims download this malware by opening an attachment or a link on the device that includes financial or other data.
The Webroot report analyzes the incidence of phishing attacks for each industry.
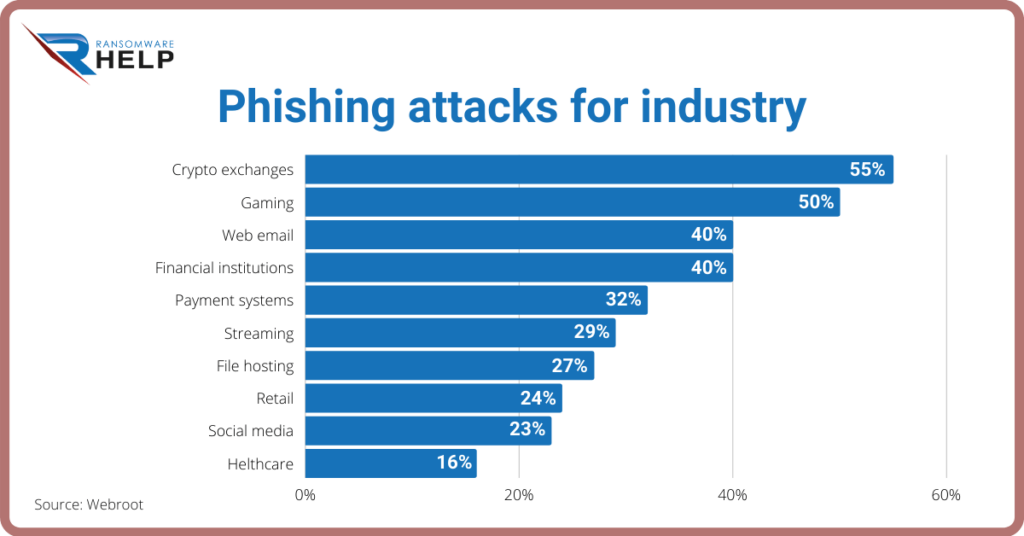
The most affected are cryptocurrency exchanges (55%) and gaming platforms (50%).
What are the types of cybercrime in Peru?
Some of the offenses related to the use of information and communication technologies that are sanctioned under the current substantive Peruvian Law on Computer Crimes and Criminal Code are the following:
- Misuse of devices and information mechanisms;
- Illegal access to computer systems;
- Sexual Harassment;
- Crimes against Intellectual Rights;
- Crimes against the Public Administration.
Cybercrime in the United Kingdom
Computer Misuse Act 1990 is the primary legislation in the UK relating to cybercrime attacks.
It lists five categories of computer misuses:
- The Unauthorized access to computer material;
- Unauthorized access with intent to commit or facilitate the commission of further offenses;
- Unauthorized acts with intent to impair the operation of a computer. The offense is committed if the person behaves recklessly;
- Unauthorized acts (section 3ZA) causing or creating a risk of serious damage. This section is aimed at those who seek to attack the critical national infrastructure;
- 5. Making, supplying, or obtaining articles for use in an offense under sections 1,3, or 3ZA.
Cybercrime in the United States
Title 18 of the United States Code, sect. 1030 referring to fraud and related activity in connection with computers punishes whoever:
- Has accessed a computer without authorization or exceeding authorized access, and have obtained information that could be used to the injury of the United States;
- Intentionally accessed a computer without authorization or exceeded authorized access, and thereby obtained financial information from any US institution or any protected computer;
- Intentionally accessed without authorization any non-public computer of a department or agency of the United States, that is exclusively for the use of the government;
- The Knowingly accessed a protected computer to defraud and obtain anything of value;
- Knowingly accessed to a protected computer and caused the transmission of a program, information, code, or command, and as a result, intentionally caused damage or loss;
- Knowingly accessed with intent to defraud traffics which affect interstate or foreign commerce;
- Intend to extort from any person any money or other thing of value and threat to cause damage to a protected computer.
What is cybercrime in Colombia?
In Colombia, Law 1273 of 2009 deals with cyber offenses.
The reform of the Criminal Code has brought to the creation of a new document for information and data protection.
This law refers to attacks against the confidentiality, integrity, and availability of data and information systems.
How to report cyber-attacks in the UK?
Action Fraud is the UK’s national service run by the City of London Police working alongside the National Fraud Intelligence Bureau (NFIB).
Immediate Ransomware Help
Don’t let ransomware hold your business hostage. Our experts are ready to recover your data and secure your systems.
Only individuals, public bodies, and not-for-profit organizations can report offenses committed online by phone or through the online reporting tool.
After registering and logging in, you will have access to a dashboard. You will be able to track, save and resume a partial report.
Businesses, charities, or other organizations currently suffering a cyber-attack can only ask for assistance by phone since online reporting is not allowed.
Moreover, under the General Data Protection Regulation (GDPR) rules, it is mandatory that you also report data breaches to the ICO within 72 hours.
How to report cyber-attacks in the United States?
In the USA, victims of internet fraud or cybercrime can report to the Internet Crime Complaint Center IC3 or send an online request to the FBI by filling this form.
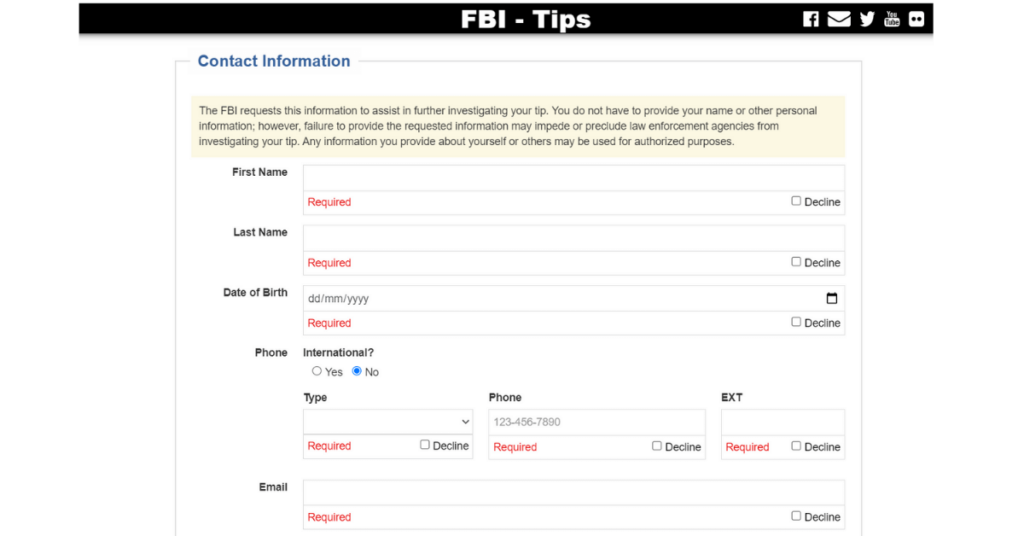
You may also report scams and fraud to the state consumer protection office, report to the local police or federal government. However, agencies usually don’t follow up and can’t recover lost money.
While state authorities offer the option to report cybercrime, it might be a slow process, just as the times of justice.
In the event of ransomware attack or cryptolocker versions attack, the best option available to you is to contact a specialized company, such as HelpRansomware.
This type of malware prevents users from accessing their files and devices and requires an anonymous online payment in exchange for access.
HelpRansomware allows you to recover encrypted files from multiple devices.
Our team of cybersecurity experts takes quick and efficient action to recover documents infected with malware.
How to report cybercrime in Uruguay?
The Montevideo Police Headquarters, through the Departamento de Delitos Tecnológicos (Department of Technological Crimes), is charged with tackling computer crimes.
Users can contact this unit via the web, email, or telephone number.
Cybercrime: laws and regulations in the UK
As mentioned above, the Computer Misuse Act 1990 is the main UK legislation that deals with offenses or malicious attacks against computer solutions.
We may find other indications in the following laws:

Immediate Ransomware Help
Don’t let ransomware hold your business hostage. Our experts are ready to recover your data and secure your systems.
- Data Protection Act 2018, including UK GDPR (EU law) that also sets out data protection requirements for immigration and other areas of law;
- Communications Act 2003, including cybersecurity obligations;
- Privacy and Electronic Communications Regulations 2003, applying to public electronic communications service providers;
- The Network and Information Systems Regulations, imposing obligations on operators, or essential services and digital service providers;
- The regulation of Investigatory Powers Act 2000 that governs surveillance and interception of communications data;
- ● The Computer Misuse Act 1990, listing cybercrime offenses which may be prosecuted in conjunction with violations under the Theft Act 1968 and the Fraud Act 2006;
- Official Secrets Act 1989.
Cybercrime: laws and regulations in the USA
In the United States, cybersecurity laws and regulations are enacted both at the federal and state level, while strict data protection rules have also been established for healthcare and banking.
The most prominent acts are the:
- Federal Computer Fraud and Abuse Act, 18 USC sect. 1030 is the primary statute providing for criminal and civil penalties;
- Electronic Communications Protection Act protects communications in storage and transit;
- Cybersecurity Information Sharing Act of 2015 (“CISA”);
- Gramm-Leach-Bliley Act of 1999 (GLBA);
- Health Insurance Portability and Accountability Act (HIPAA) of 1996.

Expert Ransomware Removal
Our certified professionals have over 25 years of experience in ransomware removal, data recovery, and computer security.
What is the penalty for cybercrime?
Cyber sanctions in the UK depend on the type of threat or attack.
According to regulation 30 of The Cyber Regulations 2020, a person who commits an offense under any provision related to Finance or licensing offenses is liable:
- On summary conviction, to imprisonment for a term not exceeding 6-12 months or a fine (or both);
- On conviction on indictment, to imprisonment for a term not exceeding 7 years or a fine (or both).
A person who commits an offense against confidentiality is liable on the same sanctions, while the imprisonment term cannot exceed 2 years or a fine (or both).
In case of information offenses, cybercriminals are liable on summary conviction to imprisonment for a term not exceeding 6 months or a fine (or both).
As for the USA, the penalties for conspiracy to violate or for violations or attempted violations are imprisonment for not more than one year and / or a fine of not more than $ 100,000 ($ 200,000 for organizations) for the first offense.
For all subsequent convictions, fraudsters are liable on imprisonment for not more than 10 years and / or a fine of not more than $ 250,000 ($ 500,000 for organizations).
Conclusions
Cybercrime is an act perpetrated over the Internet, punishable by law. We can draw the following conclusions from this guide:
- Cybercrime consists of insults, slander and online threats, child pornography, fraud, internal security, piracy, etc.;
- Phishing is a method used by cybercriminals to access user data;
- Several countries are enforcing new laws and creating specific police units to tackle cybercrime.
Attacking a computer system through a virus such as ransomware is considered a cybercrime.
Therefore, the best alternative to getting a formal police report is contacting a company specializing in cybersecurity.
HelpRansomware helps you to recover data safely, in a short time and in full respect of your privacy.

Expert Ransomware Removal
Our certified professionals have over 25 years of experience in ransomware removal, data recovery, and computer security.