In many organizations, ransomware isn’t detected when it first enters the system, but rather when it has already crippled critical systems. By then, the impact is not just technical: operations are halted, customers are affected, regulatory pressure increases, and reputational damage is widespread.
Ransomware is no longer an isolated, opportunistic attack. It’s a structured, professionalized, and highly profitable criminal model. Gangs operate with technical support, specialized negotiation, and affiliate programs.
Preventing ransomware in businesses today doesn’t simply mean installing more tools. It means reducing the attack surface before an attacker finds an opening.

Expert Ransomware Removal
Our certified professionals have over 25 years of experience in ransomware removal, data recovery, and computer security.
Ransomware as a strategic business threat
Understanding what ransomware is just the starting point. Today’s threats combine encryption, data theft, and public pressure.
The different types of ransomware show how the threat has evolved towards targeted attacks, where attackers analyze the organization’s infrastructure and ability to pay beforehand.
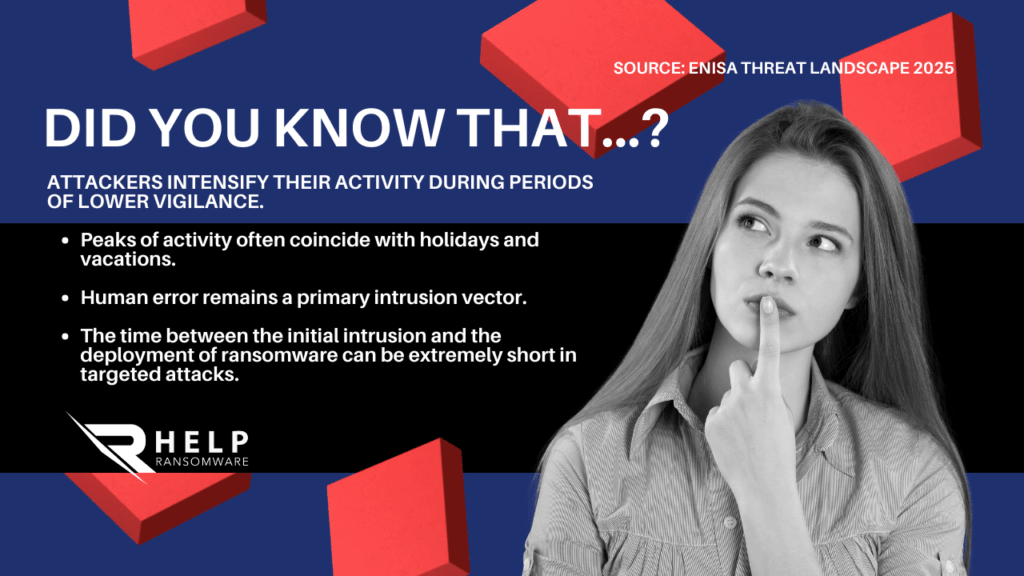
ENISA Threat Landscape 2025 report confirms that ransomware remains one of the most relevant threats in Europe, affecting both large corporations and SMEs integrated into digital supply chains.
The question is no longer whether a company can be objective.
The question is whether it is prepared.
Why many companies remain vulnerable
Many incidents begin with phishing and ransomware campaigns, credential theft, or social engineering.
Attackers don’t need extremely sophisticated vulnerabilities if they find employees without adequate training or systems with weak authentication.
Infrastructure without segmentation and excessive access
CISA‘s official Stop Ransomware guide states that the absence of multi-factor authentication, network segmentation, and proper privilege management facilitates the internal spread of the attack.
When an initial access is not contained, the lateral movement multiplies the impact.
Essential technical measures to prevent ransomware in businesses
Effective prevention is based on a multi-layered architecture.
Multi-factor authentication and identity control
Mandatory implementation of MFA significantly reduces the risk associated with compromised credentials. Dividing the network into independent segments and limiting privileges prevents an initial intrusion from compromising the entire infrastructure.
Business data protection should include offline, immutable, and regularly tested backups.
Advanced prevention: detect before encryption
Encryption is the final stage of the attack. Before reaching that point, the attacker has performed reconnaissance, exfiltration, and privilege escalation.
Having ransomware detection systems based on behavioral analysis allows you to identify anomalous activity before the damage becomes irreversible.
IBM Cost of a Data Breach 2025 report, organizations that detect and contain incidents early significantly reduce the financial impact compared to those that react late.
Speed becomes the new security perimeter.
Governance and leadership: prevention starts in the executive committee
Digital resilience cannot be delegated exclusively to the IT department.
The World Economic Forum publications emphasize that cyber risk must be integrated into the strategic agenda of the board of directors.
Having a cyberattack response plan in place before an incident occurs allows you to:
- Reduce improvisation
- Accelerate critical decisions
- Minimize reputational impact
Real prevention happens before the incident.

How to build comprehensive protection against ransomware
An effective model combines three dimensions:
1. Technology
MFA, segmentation, continuous monitoring, and protected backups.
2. Organization
Regular training, crisis drills and access reviews.
3. Strategy
Continuous risk assessment, executive leadership, and advance planning.
If your organization hasn’t yet reviewed its prevention architecture, now is the time to do so. Being proactive reduces impact, cost, and reputational damage.
Conclusion
Preventing ransomware in companies is not about adding more software, but about integrating resilience into the organizational culture.
Organizations that combine strong technical controls, continuous training, and strategic leadership are better prepared to face an environment where threats are constantly evolving.
The difference is not in who has more tools, but in who is prepared before the attack occurs. Prevention can’t be improvised once an attack has already begun.
At HelpRansomware, we work to strengthen your ransomware prevention, detection, and response capabilities, helping organizations reduce risks, protect their data, and act quickly when every minute matters.
The difference between a crisis and a controlled outage begins long before the attack.

Fast & Guaranteed Recovery
HelpRansomware provides a 100% guaranteed ransomware removal and data recovery service, with 24/7 worldwide assistance.
Frequently Asked Questions (FAQ)
How to effectively prevent ransomware in businesses?
Implementing a comprehensive strategy that combines technical controls, staff training, and executive governance.
Is an antivirus enough?
No. Modern ransomware requires multi-layered defense and continuous monitoring.
What is the main entry point?
Phishing and misuse of credentials remain common vectors.
Do backups guarantee complete protection?
Only if they are isolated and checked periodically.
Does early detection reduce the impact?
Yes. Detecting before encryption significantly reduces the total cost of the incident.
Should the executive committee be involved?
Yes. Digital resilience is a strategic responsibility.



