Descubre cómo funciona y se propaga el ransomware LockBit. Cómo se procede a la eliminación, desencriptación y recuperación de datos.

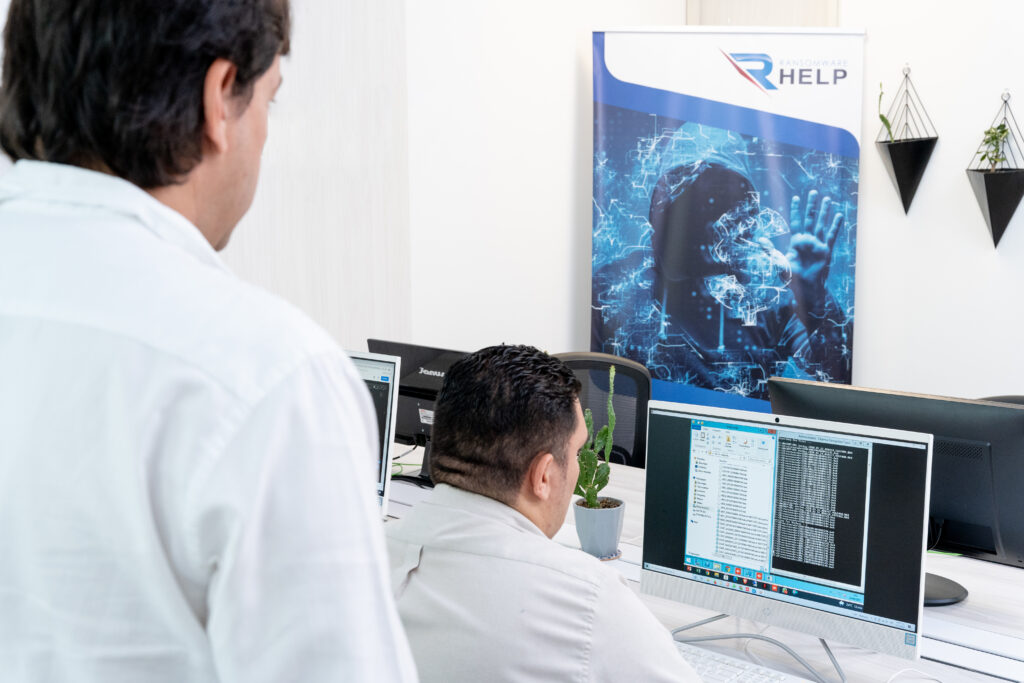
Especialistas en Eliminación de Ransomware
Nuestros profesionales certificados cuentan con más de 25 años de experiencia en la eliminación de ransomware, recuperación de datos y seguridad informática.
¿Qué es el ransomware LockBit?
LockBit es un ransomware que forma parte de la categoría RaaS o ransomware as a service.
En concreto, se trata de un criptovirus de la familia Cryptolocker diseñado con el objetivo de robar datos sensibles de las víctimas que se devuelven solo después de haber pagado el rescate.
También conocido como el virus ABCD, comenzó a propagarse en septiembre de 2019.
Es un ransomware que se dirige a empresas en lugar de particulares.
Uno de los ataques más recientes y desastrosos del ransomware LockBit se lanzó el año pasado contra Accenture, el gigante irlandés de consultoría estratégica y gestión.
Según la investigación realizada por Palo Alto Networks’ Unit 42, la variante de LockBit 2.0 tiene el número más significativo de víctimas conocidas: 850.

Esta cifra, sin embargo, no tiene en cuenta la gran cantidad de empresas y personas que no hacen públicos los ataques de ransomware para no comprometer la imagen.
De hecho, circulan números mucho mayores en los sitios del grupo de hackers, con un total de 12.125 víctimas.
Definición LockBit
Al ser un ransomware, LockBit entra en la categoría de malware.
Es responsable de ese tipo de ciberataques que tienen como objetivo la extorsión.
Después de iniciar sesión en su ordenador, este software malicioso cifra los archivos y los hace inutilizables.
Ransomware LockBit 2.0
Tras el cambio de nombre en julio de 2021, el grupo de hackers responsable de LockBit lanza una nueva extensión.
El nuevo malware mejora algunas de las características de su predecesor para ofrecer ataques más efectivos.
Ante la peligrosidad de LockBit 2.0, el FBI publicó, a principios de 2022, un documento que advierte sobre el potencial de este ransomware:
“LockBit 2.0 se describe mejor como una aplicación de ransomware muy confusa que aprovecha las operaciones bit a bit para decodificar cadenas y cargar módulos necesarios para evadir la detección. Al iniciarse, LockBit 2.0 decodifica las cadenas y el código necesario para importar los módulos requeridos […]. Al comienzo de la infección, Lockbit 2.0 elimina los archivos de registro y las instantáneas que residen en el disco».
Una vez instalada en el dispositivo, la versión LockBit 2.0 encripta todos los archivos guardados en el disco local y remoto, pero evita aquellos asociados con las funciones principales del sistema.
Cuando ha completado sus acciones, se elimina del dispositivo y activa el módulo de persistencia cuando se inicia el PC.

Especialistas en Eliminación de Ransomware
Nuestros profesionales certificados cuentan con más de 25 años de experiencia en la eliminación de ransomware, recuperación de datos y seguridad informática.
Grupo de LockBit ransomware
LockBit pertenece al grupo de crypto ransomware.
Otro ejemplo de esta categoría de virus es el ransomware Sodinokibi.
El criptoransomware es el tipo más común de ransomware: al comienzo de su propagación, atacaba dispositivos a través de aplicaciones de mensajería instantánea.
Los métodos de ataque hasta la fecha incluyen muchas más estrategias, pero el objetivo siempre es cifrar los archivos de la víctima.
El ransomware más famoso de esta familia es CryptoLocker, que ha revolucionado el mundo de los delitos informáticos desde que apareció en escena.
Según informa PurpleSec, en 2021, la variante de CryptoLocker denominada Poenix, se confirmó como la tercera en cuanto a facturación, con 55 millones de dólares.

Le precede Conti ($175 millones) y DarkSide ($80 millones).
¿Cómo funciona el ransomware LockBit?
LockBit es un ransomware que actúa de manera específica.
A diferencia de muchos otros ransomware que actúan a través de campañas de spam, este estudia y elige a sus víctimas.
Su lógica de funcionamiento se centra en ciertos pasos de rápida sucesión:
- Bloqueo de operaciones rutinarias realizadas por la PC;
- Robo de datos confidenciales relevantes;
- Intento de extorsión por una suma de dinero.
El último punto es típico de todo ransomware: los hackers piden un rescate a cambio de la clave de descifrado que permite restaurar el sistema operativo de los PC infectados.
Si la empresa decide no pagar, los delincuentes amenazan con publicar todos los archivos online, especialmente los confidenciales.
La evolución de este virus, LockBit 2.0, es un ransomware que también infecta el PC a través de campañas de phishing.
¿Cómo se propaga el ransomware LockBit?
Las formas en que se propaga el ransomware LockBit son casi siempre las mismas.
Sus objetivos suelen ser medianas y grandes empresas.
Según datos recogidos por Trend Micro, los sectores más atacados son sanidad, educación y tecnología.

Los números hacen referencia al período comprendido entre el 1 de julio de 2021 y el 20 de enero de 2022, y hacen referencia a las amenazas detectadas por el software de la organización.
De esta forma, los ataques dirigidos se convierten en en cadena: una vez que ingresa a la red, LockBit infecta todos los dispositivos conectados a él.
Una vez que la infección se propaga, este ransomware puede cifrar cualquier sistema informático accesible a través de una red.
En el caso de las empresas a las que se dirige este ataque de ransomware, los hosts se infectan primero.
Posteriormente, LockBit consigue reconocer otros similares y, tras conectarlos, la infección se propaga a través de un script.
Todo sucede automáticamente, sin necesidad de intervención humana.
Para alcanzar plenamente sus objetivos, los piratas informáticos que utilizan LockBit recurren a herramientas predefinidas, como Windows Powershell y Server Message Block (SMB).
¿Quién utiliza LockBit?
El grupo criminal detrás de LockBit tiene su sede en Europa del Este.
Como en el caso de otros RaaS, los afiliados retienen del 70% al 80% de las ganancias de los ataques, mientras que los desarrolladores de LockBit se quedan con el resto.
Recientemente se lanzó una especie de call to action para reclutar nuevos afiliados, el primer programa para subsanar errores.
El objetivo es sobre todo descubrir las vulnerabilidades del virus, para poder solucionarlas y hacerlo más efectivo.
A partir de febrero de 2020, LockBit reveló al mundo su peligrosidad.
Un informe elaborado por Interpol confirma este hallazgo al explicar que durante la primera fase de la pandemia se llevó a cabo una campaña masiva de ransomware LockBit en el continente americano.
Esto se dirigió principalmente a las medianas empresas.
Dentro de estas organizaciones, los piratas informáticos encuentran el objetivo perfecto para sus ataques.
En general, se trata de empresas que no pueden permitirse una interrupción de los servicios y, por lo tanto, pagan el rescate de inmediato.
En mayo de 2022, según un análisis realizado por NCC Group, LockBit era el ransomware más extendido.

LockBit fue responsable del 40% de los ataques ese mes, seguido de Conti.
Fases del ataque LockBit
Los TTPs (técnicas, tácticas y procedimientos) desarrollados para atacar a las víctimas son muchos.
En general, se pueden identificar fases recurrentes en el ataque del ransomware LockBit:
- Explotación: el ransomware explota las credenciales utilizadas varias veces en diferentes plataformas o vulnerabilidades como ProxyShell;
- Ejecución: a través de acciones programadas, LockBit se ejecuta mediante líneas de comando en una ventana oculta;
- Persistencia: las cuentas comprometidas pueden usarse para mantener el acceso a la red o, en casos excepcionales, se crean específicamente para este propósito;
- Escalada de privilegios: LockBit fuerza los privilegios de la aplicación, ignorando los controles del usuario;
- Evasión de la defensa: para evitar atraer la atención de la víctima y llevar a cabo su ataque sin ser molestado, este ransomware utiliza ventanas ocultas y desactiva el software anti ransomware;
- Exfiltración: en algunos casos, LockBit 2.0 limitará el tamaño de la transferencia de datos para escapar del radar de cualquier servicio de monitoreo que un usuario pueda haber configurado;
- Impacto final: en este punto, los datos se cifraron y los delincuentes exigen un rescate para enviar la clave de cifrado.
Las fases del ataque se considerarán a continuación.
Explotación
En la primera fase del ataque, LockBit escanea la red con el objetivo de buscar puntos débiles.
En general, los ataques de ransomware hacen uso de la ingeniería social para infectar a las organizaciones.
Sin embargo, como muestra el informe de Proofpoint, el 95% de las organizaciones se infectan mediante ataques de fuerza bruta.

De estos, en el 32% de los casos, los hackers lograron comprometer los servidores de la nube en el que se alojaban los datos.
Con LockBit, los piratas informáticos fuerzan el Remote Desktop Protocol (RDP) que les permite conectarse, acceder y controlar datos en un host remoto, pero como si lo estuviera haciendo localmente.
Las aplicaciones públicas como ProxyShell y Windows SysInternals PsExec, utilizadas tanto en tiempo de ejecución como en persistencia, se utilizan principalmente para lanzar ataques.
Infiltración
Cuando el hacker ingresa a través de ProxyShell, los webshells se convierten en un punto de acceso cómodo.
LockBit 2.0 tiende a usar una herramienta de omisión de control de cuentas de usuario (UAC) de Windows.
En la página de Microsoft dedicada al tema, UAC se describe como:
“Un componente fundamental de la visión global de seguridad de Microsoft”.
Esta herramienta, de hecho, permite al usuario administrar el consentimiento para el acceso a las diversas aplicaciones que se ejecutan en el PC.
Si logras forzar este token, el usuario no tiene control sobre las actividades de su dispositivo y el hacker tiene acceso a toda la información.
A partir de este momento, LockBit comienza a actuar con la más absoluta autonomía.
El verdadero propósito de esta segunda fase es dificultar o impedir la recuperación automática del sistema.
En primer lugar, por tanto, procedemos a la desactivación de todos los programas de seguridad, empezando por el antivirus.
Se basa en la preocupación de las víctimas que se dan por vencidas y pagan el rescate o publican datos confidenciales y esenciales para la empresa online.
Casi todas las víctimas, queriendo a toda costa restaurar archivos cifrados y devolver el sistema operativo a la normalidad, se muestran inclinados a pagar.
HelpRansomware, por su parte, señala que es de vital importancia no pagar el rescate.
Muchos delincuentes no entregan la clave de descifrado después del pago, por lo que no resolverá el problema y solo te mostrarás como un blanco fácil.
Implementación
En la tercera y última fase, la implementación, también conocida como infiltrate deployment, se verifica la carga útil de cifrado.
La peligrosidad del criptovirus en cuestión se encuentra precisamente en esta fase.
Se alcanzan e infectan todos los PC de la empresa, y desde allí se atacan todos los dispositivos conectados a la red.
Una vez ejecutado, LockBit bloquea todos los archivos del sistema y se libera un documento que contiene la nota de rescate dentro de cada carpeta.
Para salir de este callejón sin salida, es necesario insertar una clave de descifrado personalizada.
Recuerda: no ceder al chantaje, no pagar el rescate.
Según el informe anual de Veeam, el 48% de las empresas que sufrieron un ataque de ransomware no pudieron recuperar sus datos.

Contacta con los especialistas de HelpRansomware antes de que sea demasiado tarde: el equipo se especializa en la eliminación de ransomware y la recuperación de datos cifrados.
Tipos de amenazas de LockBit
Para cada familia de malware, existen diferentes tipos de ransomware y esto también se aplica a LockBit.
Desde su creación, este ransomware ha sufrido varios cambios en su código.
Este procedimiento es completamente natural y se debe al hecho de que, junto con la transformación del ransomware, también evolucionan las herramientas de descifrado de ransomware.
Los grupos de hackers, por lo tanto, para no perder ganancias y continuar atacando a las víctimas extorsionando dinero, modifican las cadenas de origen del virus para escapar del control.
Extensión .abcd
Antes de cambiar su nombre a LockBit, este ransomware se mostraba con la extensión «.abcd«.
Una vez que el PC o dispositivo estaba infectado, esta primera versión de LockBit encriptaba todos los documentos y archivos en el disco agregando la extensión .abcd.

Solo de esta forma la víctima podría ser consciente del ataque, además de la nota de rescate que el virus emitía dentro de cada carpeta de archivos.
Además, el virus eliminó datos de usuario, copias de seguridad e instantáneas.
Al principio no se sabía qué grupo de delincuentes se escondía detrás de este ransomware.
Lo cierto es que el virus demostró de inmediato su peligrosidad: grandes empresas afectadas por ransomware en todo el mundo, pero las versiones posteriores se han vuelto más sofisticadas de vez en cuando.
Extensión .LockBit
En su segunda versión, este ransomware agrega una extensión que revela su nombre: «.LockBit«.
En comparación con la variante anterior, LockBit registra algunos cambios en la gestión de aplicaciones desde el back-end.
En este caso, el ransomware no requiere que descargues el navegador Tor para la nota de rescate, sino que dirige a las víctimas a un sitio web alternativo a través del acceso tradicional a Internet.
La segunda versión de LockBit ingresa al dispositivo al forzar los permisos administrativos de las aplicaciones.
Al deshabilitar las alertas de seguridad de UAC, las aplicaciones se pueden ejecutar como administrador incluso sin el permiso del usuario.

Además, este ransomware también puede ser responsable de la doble extorsión.
Dado que el virus copia todos los archivos de la víctima, en caso de que no se pague el rescate, la víctima recibe la amenaza de publicar todos sus datos personales en línea.
.LockBit versión 3.0
Recientemente se lanzó una nueva versión del ransomware llamada LockBit 3.0.
Esta variante encripta archivos en la computadora de la víctima agregando la extensión “HLJkNskOq” a cada archivo.
El ransomware descifra las cadenas y los códigos mientras el dispositivo se está ejecutando y luego crea un mutex que le permite determinar cuándo lanzar el ataque.
También crea múltiples subprocesos para realizar diferentes tareas al mismo tiempo, para que pueda cifrar archivos más rápido.
Para obtener acceso a la base de datos del administrador de control de servicios y eliminarlos, LockBit 3.0 cambia el nombre de la API (Application Programming Interface) «OpenSCManagerA ()».

Como acción final, el ransomware cambia el fondo del dispositivo con una imagen que explica cómo proceder para descifrar archivos ransomware y pagar el rescate.
La pantalla dice que los piratas informáticos divulgarán los datos personales de la víctima si no siguen las instrucciones en el tiempo indicado.
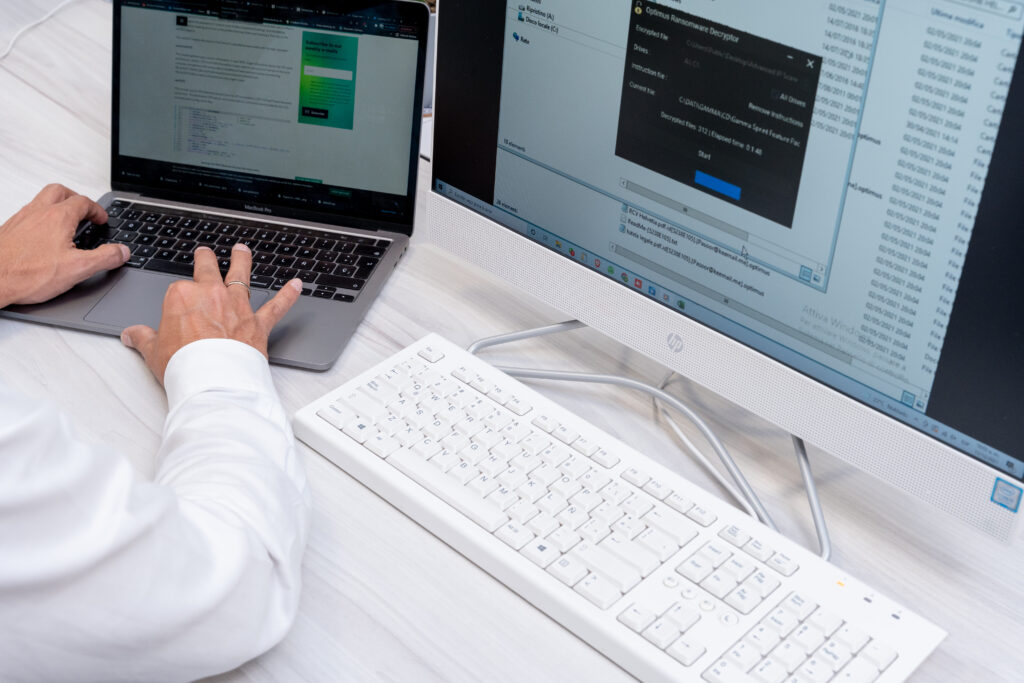
Eliminación y desencriptación de LockBit
Si has sido víctima de un ataque de ransomware LockBit, la palabra clave es celeridad.
Debes actuar rápidamente para poder recuperar archivos encriptados de tu PC u otro dispositivo afectado por este criptovirus.
La eliminación de LockBit 2.0 no es un proceso sencillo debido a la capacidad de penetración del virus.
Este ransomware puede ser difícil de erradicar porque puede ocultarse en archivos, accesos directos o configuraciones que ya están instaladas en tu ordenador.
En primer lugar, debes equiparte con un buen antimalware y antiransomware que sea capaz de encontrar todos los rastros de LockBit.
La forma mejor y más segura de eliminar ransomware es usar una poderosa herramienta de eliminación automática que ahorre tiempo y esfuerzo.
Ayuda Inmediata contra Ransomware
No permitas que el ransomware paralice tu negocio. Nuestros expertos están listos para recuperar tus datos y proteger tus sistemas.
¿Se puede desencriptar LockBit?
Como cualquier amenaza de ransomware, los datos confidenciales están dirigidos mediante un algoritmo de cifrado específico.
Estos se mantienen bloqueados hasta que se pague el rescate de la suma solicitada.
Eventualmente, el software malicioso genera un archivo de texto llamado Restore-My-Files.txt.
El archivo contiene todos los pasos que la víctima debe seguir para poder descifrar LockBit.
Los hackers deben ser contactados por correo electrónico para que puedan enviar todo el procedimiento destinado a restaurar los archivos cifrados.
Para convencer a la víctima, los piratas están dispuestos a desbloquear archivos a modo de ejemplo.
No te dejes engañar: ¡no pagues el rescate!
En la mayoría de los casos, ni el pago del rescate ni el uso de herramientas de descifrado son suficientes para abrir archivos cifrados.
Del mismo modo, eliminar el ransomware de tu dispositivo no es suficiente: incluso si logras eliminar LockBit de tu PC, no podrás recuperar sus datos.
¿Se puede descifrar LockBit 2.0?
LockBit 2.0 y su versión posterior LockBit 3.0 son más agresivos que los anteriores.
Si has sido atacado por este ransomware, tu mejor opción es consultar con especialistas ya que aún no se ha creado una herramienta de descifrado.
HelpRansomware te ofrece soluciones de ransomware, con la garantía de eliminar el virus de tu dispositivo y restaurar todos los archivos dañados.
El primer paso sigue siendo eliminar la amenaza del dispositivo, luego podría intentar restaurar tus datos recuperando la copia de seguridad.
Sin embargo, una cosa que absolutamente no debes hacer es restaurar el sistema o formatear el PC, porque de esta manera perderás cualquier posibilidad de recuperar los datos.
Cómo recuperar los datos del ransomware LockBit
El procedimiento para restaurar archivos cifrados depende del tipo de sistema activo en tu dispositivo, pero los procedimientos son similares.
Lo que leerás a continuación solo es útil si has realizado una copia de seguridad de los datos de tu dispositivo.
Si no has realizado ninguna copia de seguridad, no hay forma de poder eliminar el ransomware y descifrar archivos automáticamente.
En el primer paso, en el caso de Windows 7 y Windows XP, es iniciar el ordenador en modo seguro:
- Clica en el botón “Inicio” y presiona la tecla F8 repetidamente hasta que aparezca el menú “Opciones avanzadas de Windows” en la pantalla;
- Selecciona de la lista “Modo seguro con funciones de red”.

Con Windows 8 y 10, el procedimiento es bastante similar, deberás hacer clic repetidamente en F5.

Si no puedes iniciar tu PC en modo seguro con funciones de red, debes optar por la restauración del sistema.
De esta forma podrás recuperar los archivos guardados desde la última copia de seguridad.
¿Cómo protegerse del ransomware LockBit?
En el caso del ransomware, la prevención es la mejor defensa.
Tener un plan de protección bien definido contra esta amenaza no solo limita las posibilidades de ser atacado, sino que también reduce los daños en caso de que el ataque tenga éxito.
Para protegerse de un ransomware LockBit, sigue estos consejos:
- Ingresa contraseñas alfanuméricas complejas: se debe actualizar continuamente;
- Utiliza la autenticación de múltiples factores;
- Solicita autorización de cuenta de usuario;
- Limita el otorgamiento de privilegios de administrador a la realización de actividades específicas;
- Mantener tus cuentas activas, las cuentas inactivas son una excelente oportunidad para los hackers;
- Mantén siempre actualizadas las aplicaciones que utiliza;
- Utiliza copias de seguridad periódicas para guardar tus datos tanto online como offline: los discos duros y otros dispositivos externos son esenciales;
- Segmenta las redes para que los datos confidenciales no se concentren en un solo dispositivo.
El último informe elaborado por Entrust demuestra la importancia de una estrategia de protección de datos que incluya también el cifrado de archivos por parte de la empresa.

El 62% de los encuestados admite que su empresa tiene un plan de cifrado que se aplica a toda la compañía.
Esto también está ligado a otro aspecto que las empresas nunca deben subestimar, como es la formación del personal.
¿Qué debo hacer si mis datos están encriptados por LockBit?
Si has sido atacado por LockBit, debes saber que aún no se ha lanzado una herramienta capaz de descifrar archivos.
No obstante, hay pasos que puedes tomar:
- Toma una captura de pantalla de la nota de rescate, será útil para identificar el tipo de ransomware que te atacó;
- Reporta el delito a las autoridades competentes,
- Desconecta el dispositivo de la red: esto evitará que el virus se propague a otros dispositivos conectados;
- Apaga tu dispositivo: si bien LockBit puede continuar cifrando datos en segundo plano, este paso reduce las posibilidades;
- No te comuniques con piratas informáticos;
- Contacta con los especialistas de inmediato.
El último punto es la clave: contacta con HelpRansomware para aprovechar sus servicios de descifrado y recuperación de datos.
Conclusiones
Ser víctima de un ataque de ransomware es más fácil de lo que parece.
En la siguiente guía te hemos explicado cómo puedes protegerte del ransomware LockBit y estas son las conclusiones que puedes extraer:
- LockBit es un ransomware de criptovirus que entra en la categoría de RaaS;
- La variante LockBit 2.0 tiene el número más significativo de víctimas conocidas, 850;
- En 2021, la variante CryptoLocker Poenix se confirmó como la tercera en cuanto a facturación, con 55 millones de dólares;
- Los sectores más atacados por LockBit son los de salud, educación y tecnología;
- Las principales fases del ataque LockBit son explotación, infiltración e implementación;
- Existen varias variantes de LockBit, cada una más peligrosa y letal que la anterior;
- Es fundamental que las empresas tengan una estrategia de protección de datos que también incluya el cifrado de archivos.
En cuanto al descifrado de archivos cifrados por LockBit, es un proceso muy difícil porque no existen herramientas automáticas.
La mejor opción en este y en cualquier otro caso es contactar con especialistas.
El equipo de HelpRansomware tiene experiencia en identificar y eliminar ransomware y descifrar archivos infectados.
Ayuda Inmediata contra Ransomware
No permitas que el ransomware paralice tu negocio. Nuestros expertos están listos para recuperar tus datos y proteger tus sistemas.