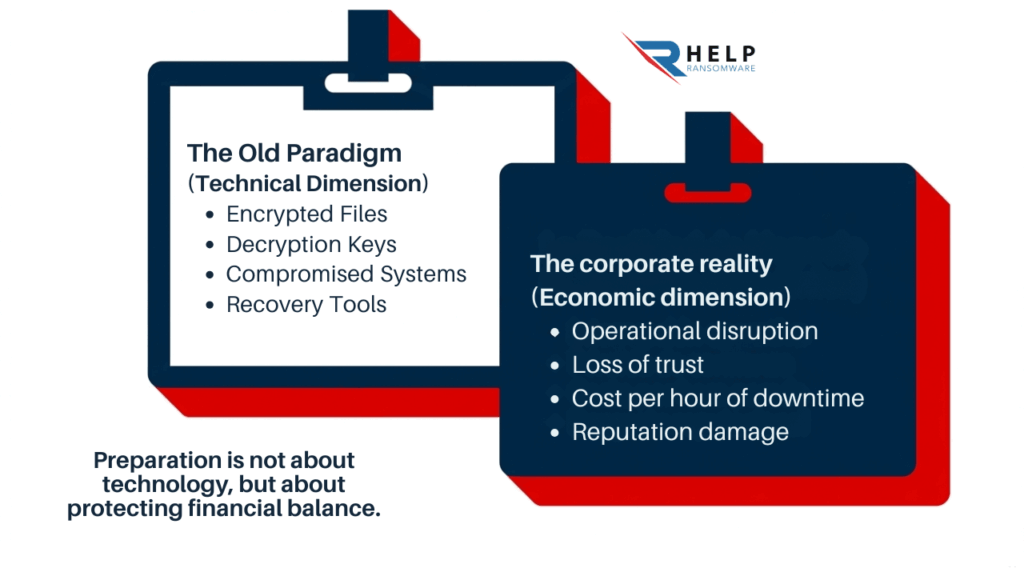
For years, ransomware has been explained in technical terms: compromised systems, encrypted files, or compromised access. However, this way of understanding the problem falls short when a company ceases operations.
Because when an attack occurs, the question isn’t technical. It’s economic.
What does it cost to stop?
What does it cost to not respond?
What does it cost to lose trust?
Translating ransomware into euros is what allows us to understand its real impact, because it is at that point where the risk ceases to be a possibility and becomes a business decision.
The big mistake: reducing ransomware to ransom
The conversation about ransomware usually revolves around a single variable: payment. It’s a visible, uncomfortable decision with clear implications. But focusing the entire analysis on that point oversimplifies the problem.
The bailout is just the beginning of the cost
The ransom demanded by the attackers is tangible, but it rarely represents the full impact. In many cases, it’s not even the most significant part.
There is already a cost before encryption. After encryption, the impact multiplies: operational disruption, recovery, communication, and crisis management.
Many companies look for immediate solutions such as ransomware decryption tools or a decryption key, but these only work in the final stage.
Ransomware is not a one-time cost; it is a chain of losses that accumulates over time.
The hidden cost: where money is really lost
There’s a part of the impact that doesn’t appear on any invoice. It’s not easily measured, but it directly affects the business.
When an organization enters a crisis, it ceases to operate normally. Teams work under pressure, processes slow down, and decisions become more reactive.
INCIBE‘s guide on ransomware highlights precisely this type of consequence, where the organizational impact outweighs the technical one.
This internal wear and tear is one of the highest costs, because it limits the actual capacity for recovery.
When the operation fails, the impact skyrockets.
Ransomware doesn’t just affect systems. It affects the ability to generate value.
Time becomes wasted money
Every minute a company is down has a cost. It doesn’t have to be a complete shutdown; it only takes certain areas to fail.
Processes that depend on systems, decisions that require data, or equipment that cannot work normally.
Ransomware turns time into immediate and cumulative economic loss.
The chain reaction: when the problem spreads
A company does not operate in isolation. It is part of an ecosystem.
When it fails, the impact extends to customers, suppliers, and partners. One delay generates further delays; an internal incident becomes an external problem.
Many companies affected by ransomware have found that the biggest impact is not the initial attack, but its spread.
Ransomware doesn’t stay inside; it spreads throughout the entire business.
The most expensive moment is not technical: it’s decisional.
One of the biggest mistakes is to analyze ransomware only from a technological perspective.
Making decisions under pressure has a cost.
During an attack, decisions are made quickly, with incomplete information and under pressure.
The decision is whether to stop, communicate, negotiate, or attempt recovery. Each decision has a direct impact on the final cost.
The problem is not just the attack, but the context in which the decisions are made.
Preparation reduces the impact, not the risk
Prepared organizations do not prevent attacks, but they manage them better.
They have processes, defined roles, and the ability to react. This reduces time, errors, and losses.
ransomware defense strategy and understanding the human factor in ransomware is key.
The difference lies not in avoiding the attack, but in how much it costs to manage it.
Reputation: The Cost That Comes Later
When the technical incident ends, the economic impact does not disappear.
Trust is an economic asset
Trust doesn’t appear in systems, but it does in results. When a company suffers an attack, that trust is affected.
Customers, suppliers, and investors react.
Loss of trust is one of the hardest costs to recover.
Medium-term impact
Reputational damage is not always immediate. Sometimes it appears later.
Fewer opportunities, more commercial difficulty, greater competitive pressure.
The European Commission has highlighted the importance of digital trust in analyses such as those on digital practices and online transparency.
Ransomware not only affects the present, it conditions future growth.
Measuring risk changes the way decisions are made
Many companies know that ransomware is a risk, but they haven’t translated that into economic impact.
From technical risk to business decision
Answering key questions changes everything:
- How much does an hour of downtime cost?
- How much is data worth?
- How much does an interruption impact?
Without this translation, the risk is underestimated.

The change of mindset
The most mature organizations don’t ask if they will be attacked.
They ask themselves:
What would it cost us to be unprepared?
This approach connects directly with understanding ransomware as a business survival problem.
If you can’t translate ransomware into euros, you’re not measuring the real risk to your company.
At HelpRansomware, we work to help you understand the economic impact of an attack, improve your response capabilities, and reduce costs before it happens.
Conclusion
Ransomware is not just a technical incident. It’s an economic problem that directly impacts business continuity.
Companies that understand their impact in euros make better decisions, react with greater control, and reduce the real damage.
Because in the end, the problem is not the attack, but how much it costs to have been unprepared.
Frequently Asked Questions (FAQ)
Is the biggest cost of ransomware the ransom?
No. Rescue is usually only one part of the total impact.
Which weighs more, the attack or the interruption?
In many cases, operational disruption is the biggest cost.
Is it possible to calculate the impact before an attack?
Yes, estimating shutdown scenarios.
Why measure it in euros?
Because it allows you to make real decisions.
Do all companies have the same impact?
No, it depends on their activity and preparation.


