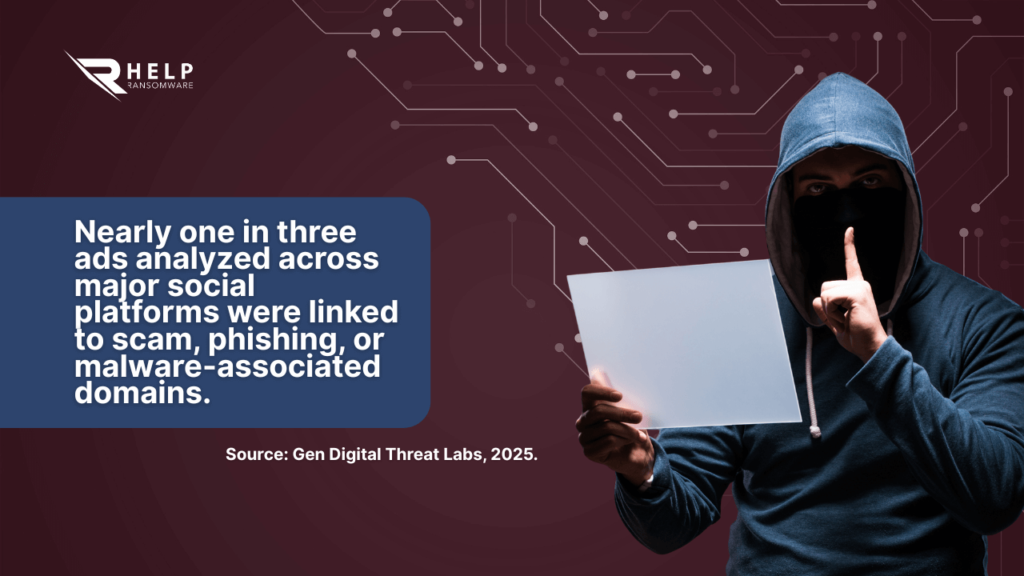
A recent large-scale investigation conducted by Gen Digital Threat Labs revealed that nearly one in three advertisements served across Meta platforms were linked to domains associated with scams, phishing campaigns, or malware distribution. The research analyzed more than 14 million ads and identified over 300 million impressions directing users to potentially harmful destinations.
The findings, later reported by Reuters, highlight a structural weakness in modern advertising ecosystems: paid social content is increasingly being exploited as a scalable delivery mechanism for cybercrime.
Malvertising — malicious advertising — is no longer confined to deceptive redirects or low-level fraud schemes. At scale, it is evolving into a practical and efficient initial access vector capable of feeding larger criminal operations.
From Social Ad to Credential Harvesting
Unlike traditional email-based attacks, malicious advertisements appear directly within trusted social feeds. Because sponsored content is perceived as platform-approved, it benefits from implicit legitimacy. Users scrolling through familiar interfaces are less likely to question a paid promotion than a suspicious email.
Many of these ads redirect victims to credential harvesting portals consistent with the tactics described in our guide to phishing. Victims are prompted to authenticate on fake portals designed to capture usernames and passwords, often using cloned branding and convincing layouts.
In other cases, advertisements trigger downloads that deploy droppers, loaders, or other forms of malware. Once executed, these payloads establish persistence, gather system information, and prepare the environment for deeper intrusion.
The transition from sponsored content to system compromise can occur in seconds.
Adversary-in-the-Middle (AiTM) and Session Hijacking Through Malvertising
One of the most technically significant evolutions in initial access campaigns is the use of Adversary-in-the-Middle (AiTM) phishing frameworks delivered via malicious ads.
Instead of simply stealing passwords, attackers now deploy reverse proxy infrastructures capable of intercepting authentication flows in real time. When a victim interacts with a malicious advertisement and lands on a cloned login portal, the infrastructure transparently forwards credentials to the legitimate service — capturing not only the username and password, but also the authenticated session token.
According to the UK National Cyber Security Centre (NCSC) 2024 Annual Review, AiTM techniques are increasingly used to bypass multi-factor authentication controls, allowing attackers to hijack active sessions without triggering traditional security alerts. This evolution changes the defensive equation.
Compromised session cookies can grant immediate access to corporate SaaS environments, email platforms, and cloud dashboards — even when MFA is enabled. From there, attackers may establish persistence, register new authentication factors, or create API keys before monetizing access through ransomware affiliates.
Malvertising becomes particularly effective in this model because it removes the friction of email delivery filters. Sponsored content appearing in trusted feeds increases the probability of interaction, accelerating session capture at scale. This is no longer about password theft. It is about authenticated access replication.

The Connection to Ransomware Ecosystems
Malvertising should not be viewed solely as consumer fraud. In enterprise environments, compromised credentials or installed malware frequently represent the first stage of a broader intrusion.
Once initial access is achieved, attackers may escalate privileges, move laterally across networks, disable security controls, and ultimately deploy encryption payloads consistent with documented ransomware attacks.
Official statistics from the FBI Internet Crime Complaint Center continue to show billions of dollars in annual losses attributed to online fraud, impersonation scams, and credential theft. These figures demonstrate how profitable early-stage compromise has become within the cybercrime economy.
As Andrea Baggio, CEO of HelpRansomware, has observed when discussing modern cybercrime supply chains:
“Initial access is no longer the most difficult phase of an attack. Criminal groups are industrializing access acquisition through multiple low-cost vectors, feeding ransomware operations with a steady pipeline of compromised credentials and infected systems.”
Malvertising fits precisely into this industrialized model. It provides scalable entry points that can later be monetized by ransomware affiliates operating within structured criminal ecosystems.

Enterprise Exposure in Hybrid Work Environments
Hybrid and remote work models have blurred the boundaries between personal browsing and enterprise access. Employees regularly access social platforms on personal devices while reusing credentials or authentication sessions tied to corporate accounts.
A malicious advertisement clicked outside the corporate network may still lead to enterprise compromise if credentials are reused or if session tokens are intercepted.
This convergence significantly expands the attack surface. Traditional perimeter defenses offer limited protection when the initial access vector originates from consumer-facing platforms embedded in daily digital behavior. Reducing credential exposure and reinforcing data governance practices are critical.
For broader defensive strategies, see our guide on the importance of protecting data.
A Structural Shift in the Threat Landscape
The convergence of paid advertising infrastructure, automated phishing kits, AI-generated scam content, and ransomware affiliate programs signals a structural evolution in cybercrime operations. Malvertising has evolved from opportunistic abuse into a structured component of the ransomware supply chain.
Security teams that focus exclusively on email-based phishing risk overlooking emerging vectors embedded directly within social platforms. Understanding and addressing malicious advertising abuse is now an essential component of modern ransomware prevention strategies.
Organizations that overlook malicious advertising as an initial access vector risk misaligning their defensive strategy with the operational realities of modern ransomware ecosystems.