When a company realizes its files have been encrypted, the attack is already over. The ransom note, the locked systems, and the operational disruption are not the beginning of the incident, but its consequence.
A ransomware attack does not happen instantly. It unfolds in stages, often without clear warning signs, exploiting legitimate access and everyday actions within the organization. The real risk is not the encryption itself, but everything that happens beforehand without being detected.
Understanding this sequence changes the approach: instead of reacting late, organizations can identify early signals while there is still room to act.

The entry point: how attacks begin without raising suspicion
In most cases, the initial access does not involve sophisticated technical exploits, but rather familiar and routine interactions.
Social engineering and deception
Attackers do not need to break systems if they can gain trust. Emails that mimic official communications, urgent notifications, or well-crafted messages are often enough to trigger action.
This type of activity aligns with trends highlighted by European authorities such as Europol in their analysis of cyber attacks, where manipulation and psychological pressure play a central role.
At this stage, the failure is not technical, but human.
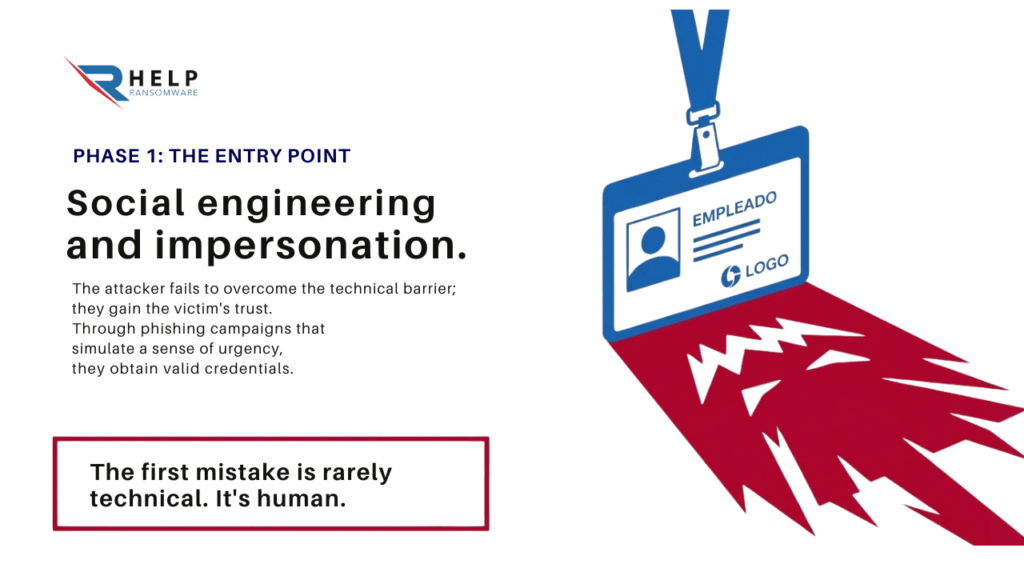
Legitimate access, invisible threat
Once the user interacts, the attacker gains access. And in many cases, that access appears completely legitimate: valid credentials, active sessions, or trusted user accounts.
This is why it often goes undetected.
This phase is closely linked to phishing, one of the most common entry points in modern attacks.
From the outside, nothing seems wrong. Internally, everything continues to operate. The attacker is inside, but the threat is still invisible.

Expert Ransomware Removal
Our certified professionals have over 25 years of experience in ransomware removal, data recovery, and computer security.
Silent phase: when attackers study the organization
Once inside, attackers do not immediately deploy ransomware. Their priority is to understand the environment.
Internal reconnaissance
During this stage, attackers analyze how the organization operates: which systems are critical, how access is managed, and where sensitive data is stored.
There is no disruption. No obvious warning signs. This lack of visibility is precisely what makes this phase so dangerous.
Much of this behavior reflects common ransomware attack tactics, where remaining undetected is more valuable than acting quickly.
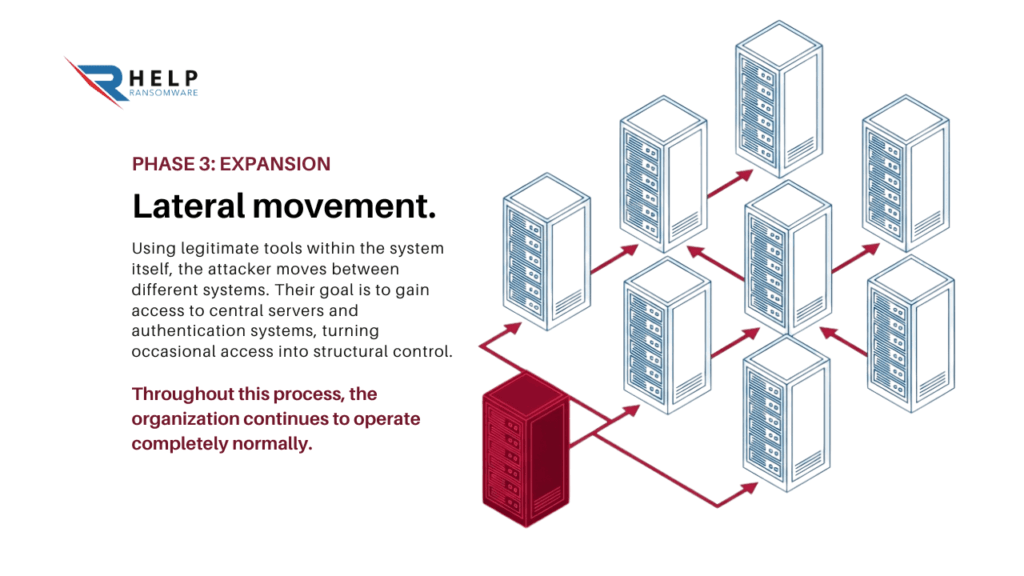
Lateral movement without detection
As attackers gain knowledge of the environment, they begin to move across the network. They rely on legitimate tools and valid credentials to avoid triggering alerts.
Their goal is to reach critical assets:
- core servers
- authentication systems
- databases
- backup infrastructures
At this point, the attack is no longer isolated. It becomes embedded within the organization’s infrastructure.
And throughout this phase, normal operations continue.
Attack preparation: when impact is carefully planned
Before launching ransomware, attackers prepare the environment to ensure maximum impact. This stage is deliberate and structured.
Persistence and control
Attackers reinforce access, analyze backup systems, and identify the most critical components of the organization.
According to European cybersecurity analyses such as those published by CERT-EU in their security advisories, modern attacks are increasingly structured, with extended preparation phases designed to maximize effectiveness.
The point of no return
By this stage, detection becomes significantly more difficult. The attacker has secured access, mapped the environment, and prepared execution.
The attack is no longer a possibility — it is waiting to be triggered.
Execution: the most visible (and latest) stage
Encryption is the moment most organizations associate with ransomware. In reality, it is the final stage.
Operational disruption
Systems stop responding, data becomes inaccessible, and business operations are interrupted. This is when the organization becomes aware of the incident.
But it is also when response options are most limited.
Early detection changes everything
This is why knowing how to identify a ransomware attack before this stage is critical. It does not eliminate risk, but it reduces impact and improves response capability.
Beyond encryption: the evolution of ransomware
Modern ransomware goes beyond file encryption. In many cases, attackers extract data before locking systems.
This introduces additional risks:
- data exposure
- reputational damage
- legal consequences
This phenomenon is linked to the increase in sextortion and online blackmail, which aim to put pressure on the victim.

Expert Ransomware Removal
Our certified professionals have over 25 years of experience in ransomware removal, data recovery, and computer security.
Where attacks can be stopped
A ransomware attack is not a single event, but a sequence. Each phase presents an opportunity for detection:
- initial access
- internal reconnaissance
- lateral movement
- preparation
The challenge is that many organizations only react at the final stage. By the time the attack is visible, it is already advanced.
If your organization is only prepared to react once systems are encrypted, it is responding too late.
At HelpRansomware, we work to strengthen early detection and response capabilities, helping organizations identify threats before they become visible incidents.
Conclusion
A ransomware attack is not a sudden event. It is a process that develops over time, often without being detected.
Organizations that understand this sequence do not eliminate risk, but they improve their ability to respond.
Because in ransomware, the difference is not reacting faster — it is recognizing the threat before it becomes visible.
Frequently Asked Questions (FAQ)
Does ransomware start with encryption?
No. Encryption is the final stage, not the beginning.
Why is it difficult to detect earlier?
Because attackers use legitimate tools and valid access, making activity appear normal.
What is the most critical phase?
The preparation phase, when attackers already control the environment.
Can an attack be stopped before encryption?
Yes, if it is detected in early stages.
Do all attacks follow this structure?
Not exactly, but most follow a similar progression.