The recent cyberattack targeting Stryker Corporation, a major U.S.-based manufacturer of medical technologies and devices, has drawn attention to a growing issue: the resilience of IT infrastructures in the healthcare and medical technology sector.
According to early reports, the incident caused a widespread outage across several internal digital systems, temporarily limiting access to some operational platforms while the company’s security teams investigated the nature and scope of the intrusion.
Although initial technical analyses did not confirm the presence of ransomware, incidents of this type often resemble the early stages of sophisticated ransomware operations, which typically begin with a silent compromise of corporate infrastructure before escalating into data encryption or extortion activities.
The Stryker case therefore illustrates how a cyberattack can quickly evolve into a full operational disruption for a highly digitalized organization, particularly in sectors where IT systems are deeply integrated into daily operations.
The Cyberattack That Disrupted Corporate Operations
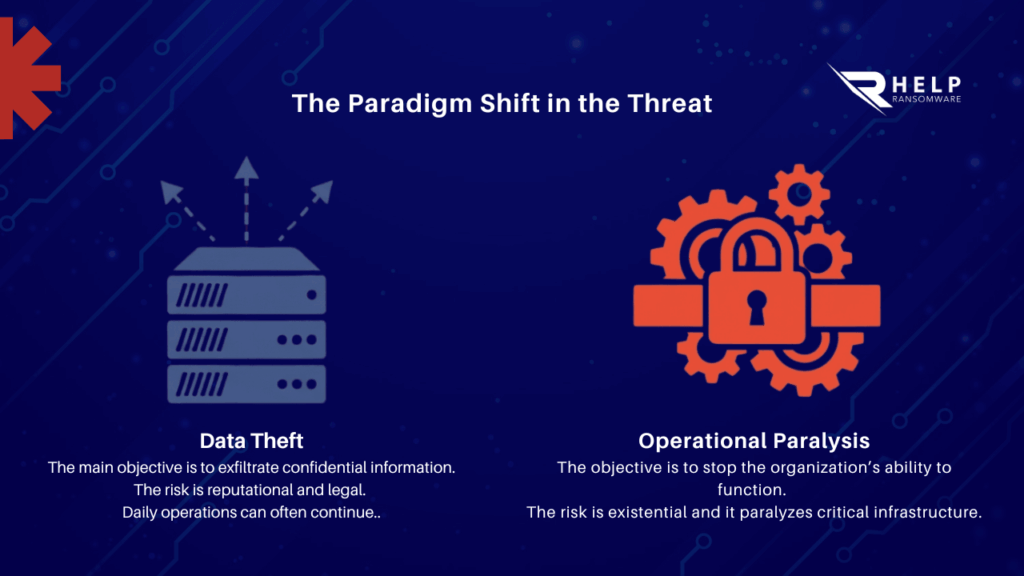
When a cyberattack hits an enterprise environment, the most immediate risk is often not data theft but the disruption of operational systems.
Corporate networks today support a wide range of critical services. When attackers compromise the infrastructure, the impact can affect multiple layers of the organization simultaneously.
Typical systems affected during large-scale cyber incidents include:
- Internal enterprise platforms.
- Cloud-based collaboration tools.
- Authentication and identity systems.
- Corporate databases and application servers.
In incidents like the one affecting Stryker, the disruption of internal systems can halt day-to-day operations while security teams work to identify the source of the intrusion and secure the infrastructure.
According to analysis from ENISA, attackers frequently remain inside corporate networks for weeks before being detected, conducting reconnaissance activities that allow them to map the internal architecture of the organization.
During this stage, attackers typically focus on identifying high-value targets such as core servers, authentication infrastructure, and backup repositories. Because these reconnaissance activities often blend with legitimate administrative actions, detecting them early can be extremely challenging for security teams.
Many organizations only realize that an intrusion has occurred when operational systems begin to fail or when attackers escalate privileges across the network. This early phase of a cyber intrusion is often associated with broader cybercrime campaigns that later evolve into full-scale ransomware attacks.
Understanding these early indicators is therefore a critical component of effective ransomware detection and long-term ransomware protection, particularly in industries where digital infrastructure is deeply integrated into operations. This is especially true in ransomware in the healthcare sector, where attacks can quickly disrupt critical systems and services.
Why a Cyberattack Can Escalate Into a Ransomware Incident
Modern ransomware campaigns rarely begin with immediate data encryption. Instead, they typically follow a multi-stage intrusion model designed to maximize the attacker’s control over the network.
The attack usually begins with initial access to the organization’s infrastructure. This may occur through:
- Software vulnerabilities.
- Compromised credentials.
- Misconfigured remote access services.
- Phishing campaigns targeting employees.
Once inside the environment, attackers begin a process known as lateral movement, allowing them to navigate across systems and escalate privileges. This phase is frequently associated with the technique known as Living off the Land, where attackers leverage legitimate administrative tools already present in the operating system. By using trusted system utilities, they can move through the network without triggering traditional security alerts.
After achieving administrative access, attackers may spend additional time identifying:
- Domain controllers.
- Centralized storage systems.
- Backup infrastructures.
- Sensitive data repositories.
Only when this reconnaissance phase is complete do attackers typically prepare the deployment of ransomware across multiple systems.
The Possible Geopolitical Dimension of the Attack
Some international reports, such as CNN, suggest that the cyberattack may also have a geopolitical context.
A pro-Iranian hacker group known as Handala reportedly claimed responsibility for the incident, stating that the operation targeted Stryker’s infrastructure as part of broader geopolitical tensions involving Iran, the United States, and Israel.
According to media reports, the attackers allegedly disrupted Microsoft-based systems used internally by the company and claimed to have exfiltrated a significant amount of corporate data. These claims have not been confirmed by official investigations. The company has stated that early technical analyses did not reveal evidence of ransomware or malware within its systems.
However, the case illustrates how corporate digital infrastructure can increasingly become a strategic target in geopolitical cyber operations, particularly when companies operate in sensitive sectors such as healthcare or medical technology.
Why Secure Backups Are Critical During Cyber Incidents
One of the most decisive factors during ransomware incidents is the availability of secure and resilient backup systems.
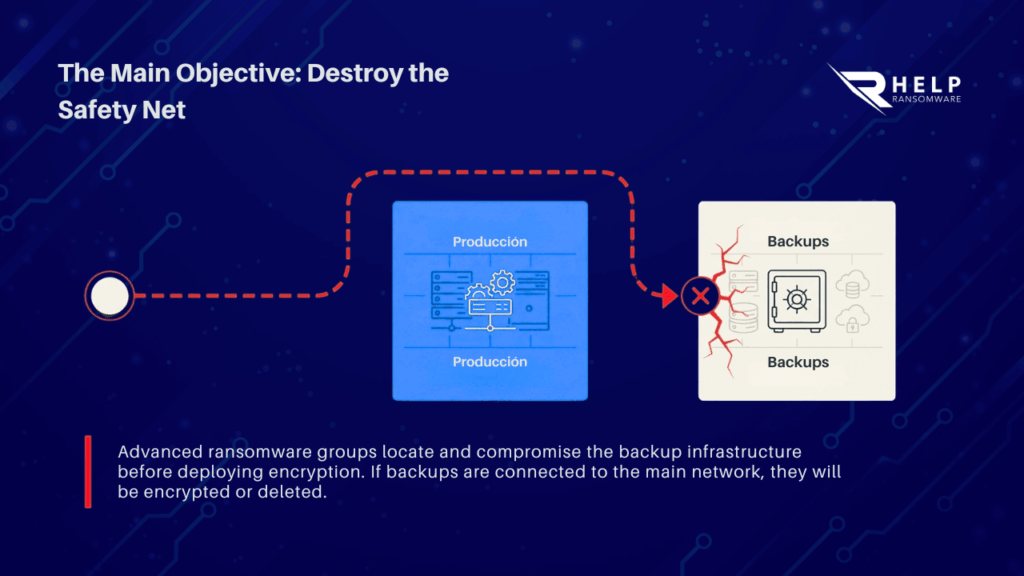
Many advanced ransomware groups attempt to locate and compromise backup infrastructures before deploying encryption payloads. If backup repositories remain connected to the primary network environment, they may be encrypted or deleted together with production systems.
To reduce this risk, modern cybersecurity strategies often rely on backup architectures that include:
- Isolated storage environments.
- Immutable backup copies.
- Segmented network infrastructure.
- Regular verification of recovery procedures.
These measures allow organizations to restore operations more quickly after a cyberattack, even in the event of severe infrastructure compromise.
The Key Lesson From the Stryker Cyberattack
The cyberattack on Stryker proves that modern threats target an organization’s very ability to function. In highly digitalized sectors like healthcare, IT disruptions halt critical operations including device management and supply chains.
“The Stryker case reminds us that modern ransomware is the final act of a silent compromise,” says Andrea Baggio, CEO of HelpRansomware. “Prevention isn’t just a wall; it’s the ability to spot the intruder while they are still measuring your house.”
Today, cybersecurity is no longer just about prevention. It is about digital resilience: the capacity to respond to incidents and restore systems as quickly as possible. HelpRansomware specializes in these critical phases, ensuring operational continuity even against the most sophisticated attacks.