This practical and easy to follow guide will help you know the definition of ransomware and what to do to remove it.
Immediate Ransomware Help
Don’t let ransomware hold your business hostage. Our experts are ready to recover your data and secure your systems.
The best way to protect your files from ransomware is to prevent malware from entering your computer.
If the damage has already occurred, do not lose heart.
While there is no simple solution, this practical and easy to follow guide will help you manage the ransomware removal.
Can the ransomware be removed?
If you want to know how to remove ransomware from your Windows PC, we have good and bad news.
The good news: it’s not easy, but it’s possible.
The bad news: it’s not always possible.
Ransomware programs and attacks are becoming more sophisticated, and as a result, victims find it harder to clean their computers and recover their files.
Depending on the type of attack, ransomware removal can range from simple to impossible.
Scareware attacks install malicious software programs that you can uninstall in minutes. Simultaneously, the more common variants, known as file coder or encryption ransomware, are much scarier because they encrypt your most precious files.
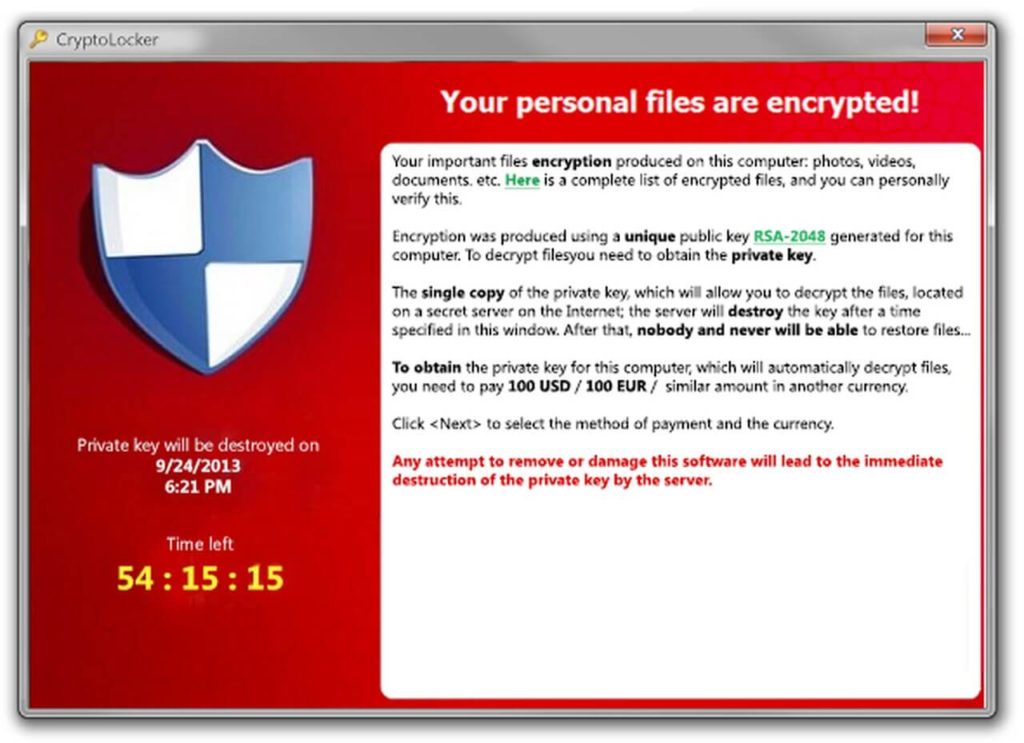
In this case, instead of deleting or corrupting your files or stealing your identity, the attacker’s encryption holds your files hostage until you pay to receive the decryption key.
Each file coder has its encryption method, which means you can’t just remove it like other malware forms.
If not, you can usually use a standard antivirus to remove them.
If you know what type of ransomware attacked your PC, you may be able to find a decryption tool to recover your files.
Furthermore, there is an aggravating criminal factor in all of this: with the promise of fast and effective decryption, some sites trick victims into downloading yet more malware.
Be wary of scammers and do not focus everything on DIY: contact the HelpRansomware experts who will be able to manage your crisis with seriousness and professionalism.

Fast & Guaranteed Recovery
HelpRansomware provides a 100% guaranteed ransomware removal and data recovery service, with 24/7 worldwide assistance.
An ounce of prevention saves your life.
You can stop ransomware from hitting you and your PC with minimal effort.
Back up your PC files and operating system (OS) regularly.
You can use a cloud storage solution like Dropbox or Google Drive for your files and a flash drive for your operating system and your files.
Whichever solution you choose, never keep your backups on the same Windows PC as the ransomware can infect them along with the originals.
If you have not avoided the attack, but have been a victim of it, follow the following steps to undo the damage.
Step 1: Isolate infected devices immediately
The first thing to do if ransomware has attacked your Windows PC is to find and disconnect all infected wired and wireless computers and other devices on your network.
This strategy will prevent the ransomware from spreading and taking multiple computers, tablets, smartphones hostage.
During this process, also disconnect everything connected to devices on your network, including:
- Shared or unshared network drives;
- External hard drives;
- USB sticks;
- Cloud storage account.
To complete this step, check if any of these connected to the infected PC.
If you suspect they were connected to a PC, you will also need to check their systems to ensure there are no ransom messages.
Step 2: identify the type of ransomware attack.
Next, find out which strain of ransomware you are dealing with – having this information could help you find a ransomware solution.
The most problematic types of attacks come via file codes such as WannaCry or CryptoLocker.
Here is a brief general overview:
- Filecoders encrypt and lock files on your PC. The cybercriminals require payment of the decryption keys usually within a deadline; otherwise, they could damage, destroy or permanently block your files. About 90% of ransomware strains are file coders.
- Scareware typically bombards your PC with pop-up ads for a fake security tool that demands payment in exchange for fixing fake PC problems.
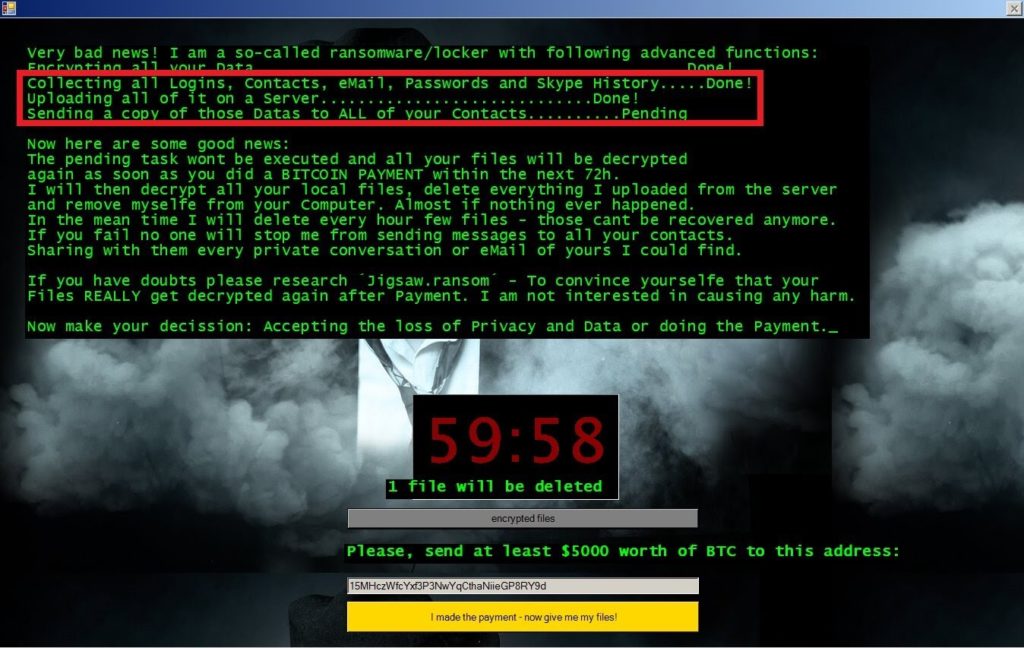
- Doxing-related ransomware involves an email or message informing you that cybercriminals have your usernames, passwords, emails, and instant messages and will make them public unless you pay a ransom.
- Screen lockers do precisely what the name implies: they lock the screen, blocking access to your device.

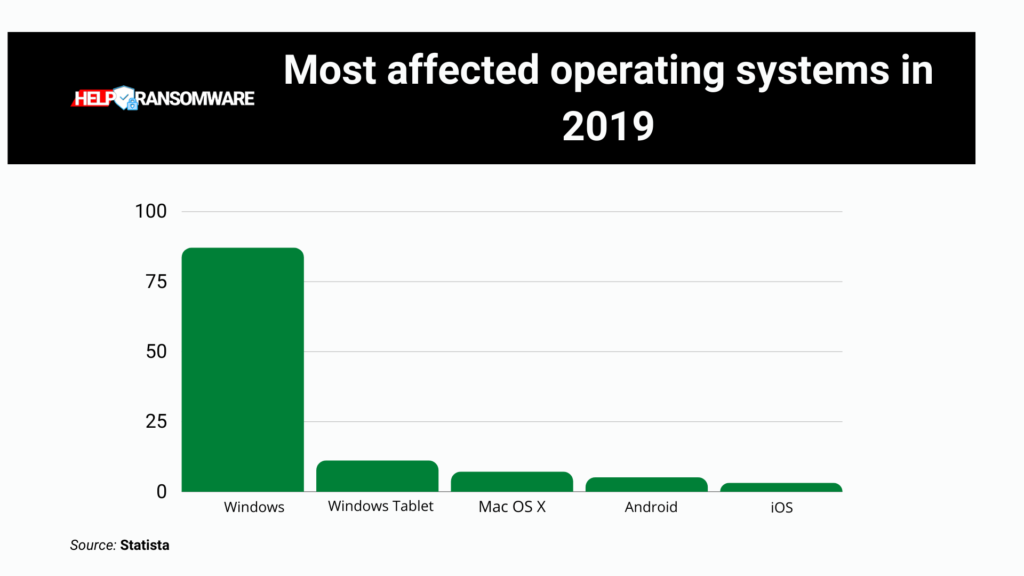
While most ransomware attacks exclusively target Windows PCs, all four of the variants listed above can infect Macs, iOS devices, and Android devices.
Use the Crypto Sheriff tool to identify the type of ransomware.
To help you determine the type of ransomware on your device, we recommend using Crypto Sheriff from No More Ransom.
This handy tool Provided by Europol’s Europol Cybercrime Center, checks the files encrypted by the attacker and the ransom note.

Expert Ransomware Removal
Our certified professionals have over 25 years of experience in ransomware removal, data recovery, and computer security.
If Crypto Sheriff recognizes the encryption and has a solution, it provides you with the link to download the decryption program you need.
Visit the technical forums to learn more about the types of ransomware.
You can also visit the PC Troubleshooting and Technical Support forums to find information on the variant of ransomware you want to remove.
Even if it’s new, you may find a thread offering a fix or a line where forum members work towards a solution.
Some ransomware infections will rename files and file extensions (for example: .exe, .docx, .dll) after they have been encrypted.
When you visit technical forums for help, look for the names and extensions of your encrypted files; each can help guide you in discussions about the strain of ransomware you wish to get rid of.
We recommend that you look in these forums:
Step 3: Remove the ransomware malware
Now is the time to get rid of the malware that is holding your PC hostage.
You have four removal options for Windows 10, 8, and 7:
- Check if the ransomware has cleared itself (which often happens).
The ransomware on your PC likely removes itself after encrypting your files. Cybercriminals don’t want their malicious software to leave clues that could help create decryption tools for that strain. You can use an antivirus to scan your computer for ransomware.
- Remove it with an antivirus
A good antivirus like Avast Free Antivirus can quickly and easily detect and eliminate many types of ransomware programs. It will also help protect your Windows PC from all kinds of cyberattacks in the future.

- Ask our HelpRansomware, technical support experts.
You can contact HelpRansomware professionals and ask them to delete the ransomware malware.
In addition to helping you remove the ransomware, the team also ensures the encrypted files recovery.
- Manually remove the malicious program
This option is only valid if you are an advanced user because quite specific skills are required. If you wish to clean your computer yourself, we recommend that you first visit the online forums we have mentioned.
We cannot provide instructions on removing all the programs behind the ransomware attacks yourself – there are too many. You will be able to learn a lot more from the experiences and guidance of the forum members.
Step 4: Restore encrypted files
Once the malware is eliminated, you are ready to restore the ransomware-encrypted files.
Here are some methods that can help you regain access to your encrypted files.
Option A: Restore the system from a backup
If you have backed up your computer’s operating system, you can quickly restore your system and files and deal with the scareware, screen locker, or file encoder that infected your PC.
Once you remove the program that prevents you from opening Windows or running any programs, the encryption will not spread across the device and network.
Although screen lockers make up the minority of ransomware cases, you should still try your device’s “System Restore” feature.
Your PC system files and programs restore to their previous state.
While the feature is enabled by default, it’s a good idea to double-check it, especially if you’re using a shared computer.
You can also try to access shadow copies of your files, which will help you restore the original versions.
If that doesn’t work, try restoring previous versions of the files.

Immediate Ransomware Help
Don’t let ransomware hold your business hostage. Our experts are ready to recover your data and secure your systems.
Windows 10 and Windows 8 have a “File History” feature that makes the process easier; Windows 7, on the other hand, requires a little more effort, but the method is still simple.
Can only use Shadow copies to recover files when dealing with a basic file coder.
In some cases, the ransomware on your PC may just have hidden your files.
In Windows 7, the path is:
- Go to “Computer”;
- Press “Alt” and select “Tools”;
- Select “Folder Options”;
- Select the “View” tab;
- Choose “Show hidden files, folders and drives”;
- Click OK.
In Windows 10 and 8 the procedure is simpler:
- Open “File Explorer”;
- Select “View”;
- Select “Hidden items”.
Finally, you can try to use CCleaner’s Recuva file recovery software, which will help you to recover deleted or lost files instead.
Option B: Use decryption tools
If you have identified the ransomware as a filecoder that encrypted your files and if you know the specific strain of the encryption, you can try to find a decryptor that can help you regain access to your files.
Unfortunately, most ransomware strains have yet to be decrypted, so in most cases there won’t be a tool capable of unlocking your files.
In this unfortunate scenario, your options are limited to restoring files from a backup (if you have one) or waiting for someone to release a free decryption tool for the particular ransomware strain on your PC.
Option C: Don’t pay the ransom and don’t trade
If you have followed all the steps we have listed and are still unable to unlock your files, we recommend that you wait for the release of a decryption tool for the type of ransomware that has infected your computer.
In some cases, cybercriminals reveal parts of their code that can help create a solution.
We understand the urgency of the situation, but we highly recommend that you don’t pay the ransom or negotiate with your PC hijacker – the payment only supports ransomware attackers, motivating them to continue their businesses and develop new strains.
In some cases, ransomware payments could also fund other illegal activities.
Finally, keep in mind that criminals don’t always remove the ransomware, unlock your computer, or give you the decryption tool for their effort when you pay them.
Most of them prefer not to damage their reputations, so they reveal the code to victims after they have paid them, but it is not uncommon for cybercriminals to collect the payment and disappear or send decryptors that don’t work.
In some cases, you may end up paying a completely different criminal.
For this, as I have already told you previously, it is essential to contact the HelpRansomware specialists, who will be able to handle the situation at 360 degrees.

Expert Ransomware Removal
Our certified professionals have over 25 years of experience in ransomware removal, data recovery, and computer security.




