Ransomware has been one of the most profitable cybercrime threats for years. However, modern attacks no longer rely only on encrypting files. Attackers are increasingly combining technical intrusions with manipulation techniques designed to pressure victims into paying faster.
One of the most concerning developments is the use of deepfakes, manipulated audio or video capable of imitating voices, faces or identities with remarkable realism.
When these techniques are combined with ransomware, the result is a new form of cyber extortion that mixes technical intrusion with psychological manipulation.
Understanding how these attacks work is essential for organizations that want to recognize threats before they escalate.
The evolution of ransomware attacks
Traditional ransomware followed a relatively simple pattern: attackers gained access to a network, encrypted files and demanded payment to restore access.
Today, the strategy has become more sophisticated. Cybercriminals often combine data theft, identity impersonation and internal manipulation to increase pressure on the victim.
In this landscape, developments related to artificial intelligence in cybersecurity have also created new opportunities for fraud. Technologies capable of generating realistic audio or video content can be used to strengthen extortion attempts during an attack.
The objective remains the same: create enough pressure for the victim to pay quickly.

Expert Ransomware Removal
Our certified professionals have over 25 years of experience in ransomware removal, data recovery, and computer security.
What deepfakes are and why they are dangerous
Deepfakes are manipulated audio-visual content capable of reproducing a person’s voice, face or gestures with high realism.
This means an attacker could generate a fake video or audio message that appears to come from a company executive, a partner or another trusted contact.
European regulatory discussions around trustworthy artificial intelligence also highlight the risks associated with manipulated digital content, as outlined in the EU framework for trustworthy artificial intelligence, which stresses the need to address misuse of synthetic media.
The real problem is not only the technology itself, but how convincingly it can be used to deceive people.
When deepfakes reinforce ransomware attacks
The risk increases significantly when manipulated content is used during a ransomware incident.
Identity impersonation
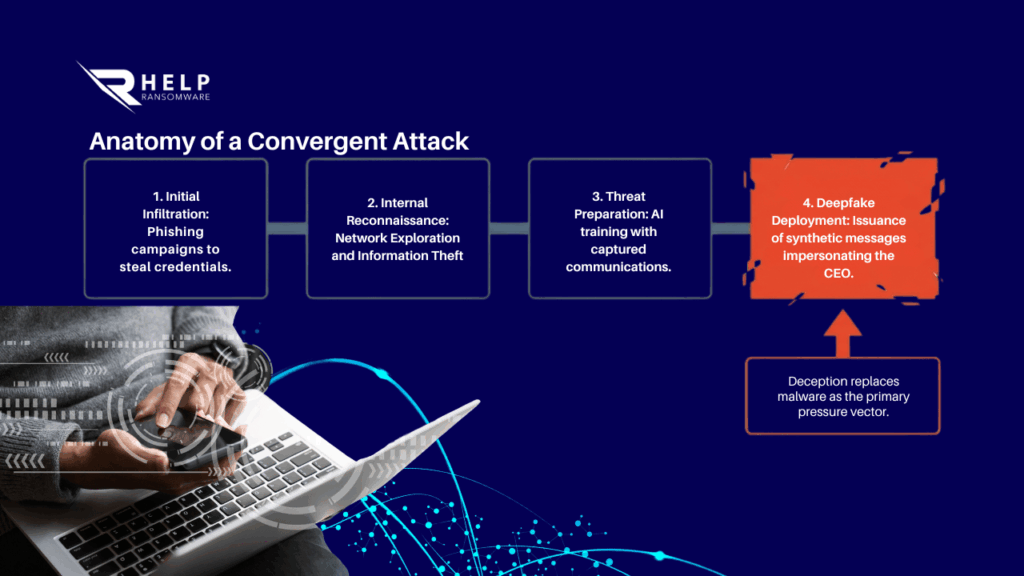
Attackers may send audio messages that imitate the voice of a CEO or executive, requesting urgent action or confirming a supposed breach.
These strategies align with many of the modern ransomware hacker tactics, where technical attacks are combined with deception.
Accelerating decisions under pressure
The goal is to force a rapid response before the victim has time to verify the authenticity of the message.
As Andrea Baggio, CEO of HelpRansomware, explains:
“Modern ransomware is no longer limited to encrypting files. Attackers combine technology and manipulation to accelerate ransom payments.”
How these attacks usually begin
In many incidents, the first stage of the attack still follows familiar patterns.
Many intrusions begin with phishing and ransomware campaigns designed to steal credentials or trick employees into granting access.
Once inside the network, attackers can gather internal information and prepare a more convincing threat.
For this reason, understanding how to identify a ransomware attack has become increasingly important for organizations.
When fraud replaces the technical attack
In some situations, attackers may not even need to execute ransomware encryption.
A convincing threat supported by manipulated content can be enough to trigger payment.
These cases are often linked to digital fraud incidents online, where deception replaces technical damage as the main strategy.
The combination of ransomware and deepfake technology demonstrates how cybercrime is evolving toward more complex and harder-to-detect attacks.
Conclusion
The convergence of deepfakes and ransomware represents a new phase in cyber extortion.
Attacks are no longer based only on technical vulnerabilities, but also on manipulating trust, identity and perception.
Organizations that understand how these tactics work will be better prepared to detect warning signs and prevent an incident from escalating into a serious crisis.

Expert Ransomware Removal
Our certified professionals have over 25 years of experience in ransomware removal, data recovery, and computer security.
FAQ
What is a deepfake in cybersecurity?
A deepfake is manipulated audio, image or video designed to imitate a real person using artificial intelligence technologies. It can be used to deceive victims or impersonate trusted individuals.
How are deepfakes used in ransomware attacks?
Attackers may generate fake audio or video messages to impersonate executives or strengthen extortion attempts during a ransomware incident.
Can deepfakes lead to corporate fraud?
Yes. Deepfakes can trick employees into transferring money, sharing credentials or granting system access if the request appears to come from a trusted source.
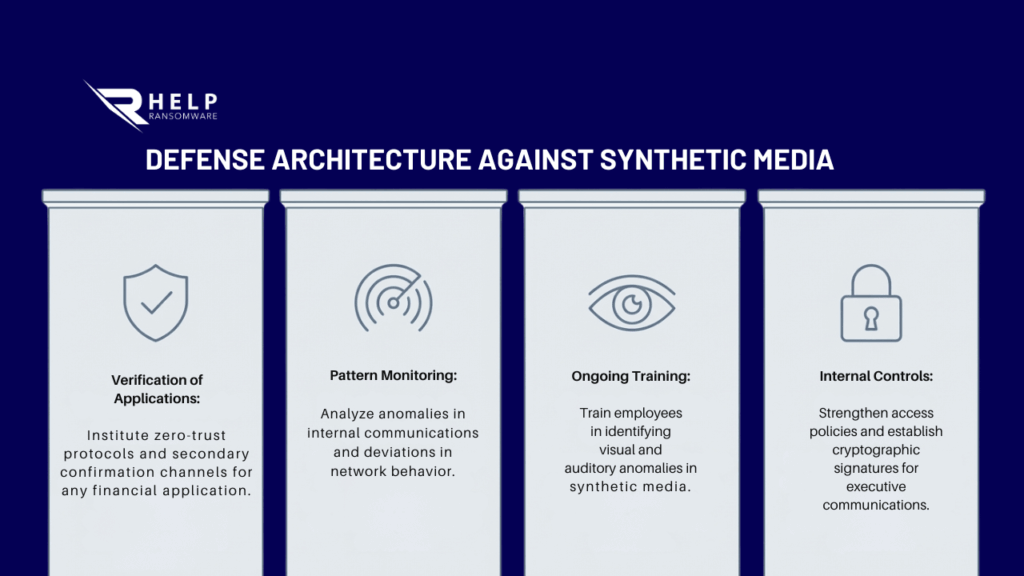
How can organizations detect these attacks?
Companies should verify urgent requests, monitor unusual communication patterns and understand how ransomware attacks typically develop.
Can deepfake-based attacks be prevented?
Training employees, verifying sensitive requests and strengthening internal security controls can significantly reduce the risk.



